Critical Thinking Within CTI
By Ken Dunham, 4D5A Security
Thursday, March 26th, 2026
All too often in 2026, analysts now rely upon tools, technology, and artificial intelligence (AI) to do the “thinking for us” instead of using our brains in the cyber threat intelligence (CTI) lifecycle. Analysts are “drowning in data” with a wealth of emails, tweets, texts, messages, feeds, and other information that all have to be read, processed, normalized, correlated, understood, and potentially weaponized into tools and technology for defensive posture. A reliance upon tools and artificial intelligence (AI) is quickly becoming the new standard, a threat to "human in the loop” and our most important asset, people!
The disciplined process of critical thinking to skillfully conceptualize, apply, analyze, synthesize, and evaluate information is critical for a human to perform throughout the CTI process.
What is Critical Thinking?
According to dictionary.com “critical thinking” is “Disciplined thinking that is clear, rational, open-minded, and informed by evidence”. Some summarize the concept as “goal-directed thinking”. According to a variety of sources, critical thinking is a process that includes the following as a constructive method and for problem solving and innovation:
-
Objective Analysis
Observation and evaluation of data and information without personal bias or emotional influence. See Structured Analytical Techniques in the curriculum for more information.
-
Questioning Assumptions
Challenge all assumptions and surface-level information for possible assumptions or incorrect information.
-
Logical Reasoning
Structured arguments based upon evidence and sound reasoning.
-
Informed Decision Making
Synthesizing and evaluating data to reach sound conclusions.
-
Questioning and acknowledging bias
Understanding one's biases and looking for information opposing what they intuitively conclude.
Outstanding critical thinkers are “thinking about how they are thinking” to continually improve (aka Metacognition). In seeking to apply critical thinking, critical thinkers continually seek to always:
- Clearly define issues, challenges, and problems
- Collect data, opinions, and arguments
- Analyze and evaluate the trust, confidence, quality, and relevance of all data and information
- Identify assumptions and bias in self and others, and sources
- Conclude a well-reasoned, evidence/data-driven conclusion
This is a dynamic, iterative process, subject to continual change within the lifecycle of CTI. Strong critical thinkers are humble at heart, able to fully reflectively consider all sides and consider where they may be biased, incorrect, or unrelated, above pride and ego.
The Core Components of Critical Thinking Within CTI
To truly practice critical thinking, you must engage in four specific mental activities:
1. Objective Analysis (Data-Driven Hypothesis)
Use your gut instincts and experience to formulate a data-driven hypothesis, using critical thinking and problem-solving as part of that:
Bad: “I think this is a threat country IP address”.
Good: “80% of initial datapoints directly overlap with a threat country actor group.”
Note: this is where Observe, Orient, Decide, and Act (OODA) Loop developed by the U.S. Air Force can be excellent for helping make fast-paced decisions in a chaotic environment, such as threat hunting to support a breach. A key component of the OODA loop is the rapid adaptation with a change in circumstances or findings as you threat hunt.
2. Skepticism ("Trust but Verify")
Critical thinkers don't trust anything blindly, always questioning where it came from, how trusted is the source and the data being reviewed, and how does it fit into the context I'm creating based upon the hypothesis I'm considering in my research and response?
- Who is the source?
- Why was it written or authored or performed?
- What are their means and motive of the actor(s) behind the event/incident?
- Does the author have bias or reason to influence the audience?
- Is this data current or outdated and/or relevance?
- How trusted is the data being reviewed, in context to the source, actor, and context?
- Why is this data or information useful in the context of my hypothesis(s)?
The analyst challenges themselves, not trusting their own thoughts and thinking or bias or that of a trusted colleague. Everything must be challenged and checked to ensure that it is true and accurate!
The analyst is on guard for Confirmation or Observer Bias, where they might be trying to make the data fit into a puzzle they want to complete instead of letting the data objectively speak for itself. If handling a complex data sets, which may generate multiple Hypothesis the analyst may employ Analysis of Competing Hypotheses (ACH) (Heuer & Pherson) approach to rule out other possible hypotheses as soon as possible, helping limit plausible theories to simplify the problem set and approach.
Analysts also challenge Cognitive Bias, where they make a bad choice that they think is a good choice. Fallacies are also looked for in this phase, where something that sounds true and is based on data is indeed false, and is then ruled out instead of being incorrectly considered true. Lastly, Availability Heuristics, where the analyst overestimates the importance of a finding of information, is also considered in reviewing data and cross-checking findings.
Self-Regulation is not always enough. In structured analysis environments, there are teams of analysts that work together reviewing the same data, and producing an individual hypothesis. If more than one analyst identifies the same hypothesis, then the likelihood of a valid conclusion increases. In smaller, less structured environments, a review by other non-analysts may be the independent challenge needed. The untrained analyst may conclude the analyst has a valid hypothesis or suggest an alternative hypothesis.
While self-regulation is critical, experienced CTI experts recognize that isn't good enough to drive integrity of outcomes, requiring quality assurance and a second set of eyes from a team member. Operationally, this often looks like analysts reviewing work for one another, on-the-job training of seniors and juniors, and similar operational strategies, to ensure self-regulation of the process and team outcomes with high assurances.
4. Logical Inference
In connecting the dots, the analyst uses deduction, induction, and abduction to logically conclude findings:
-
Deduction
General to specific
-
Induction
Specific to broad
-
Abduction
Simplest explanation (Occam's Razor philosophical principle)
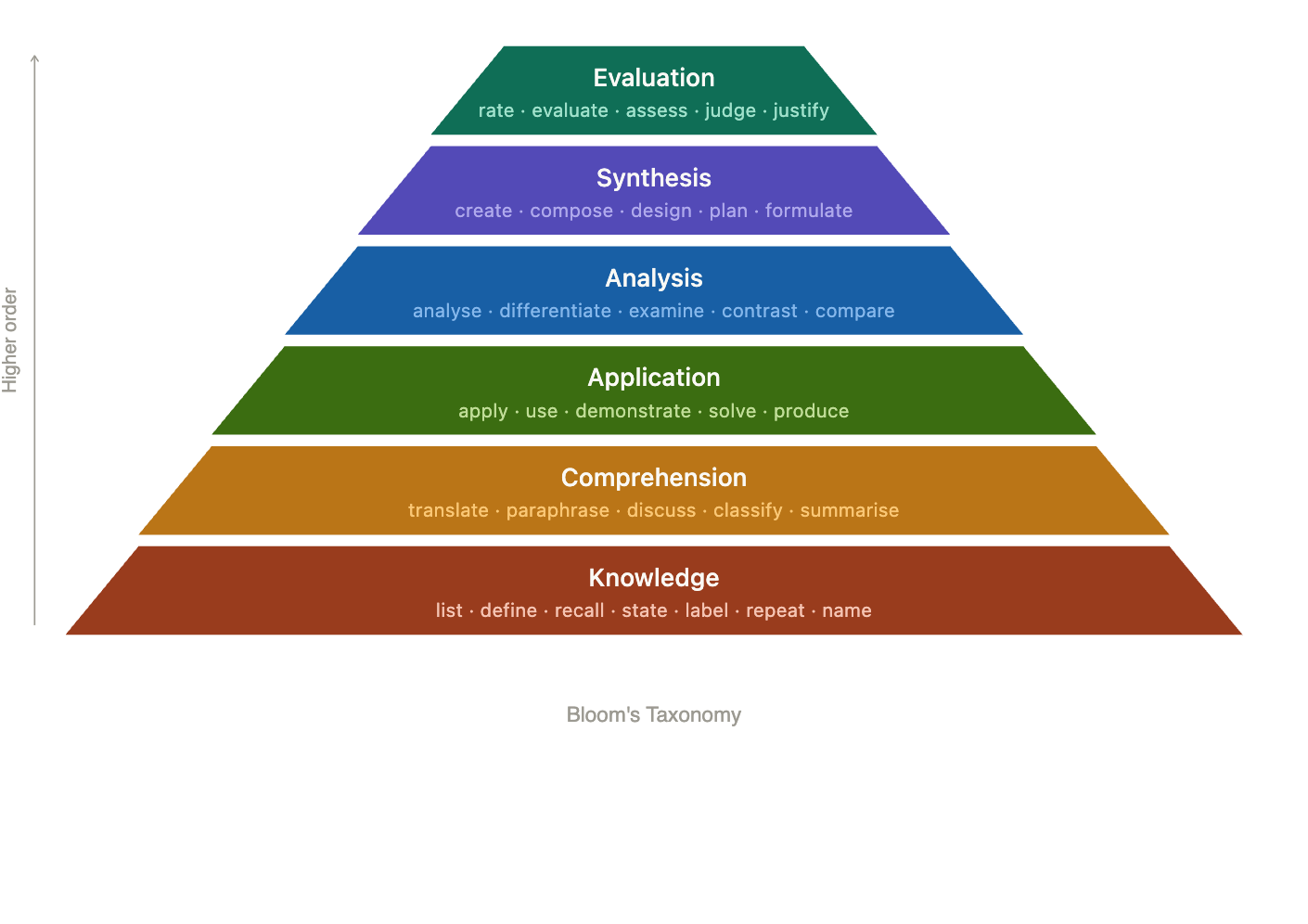
Bloom's Taxonomy
In many ways critical thinking mirrors that of Bloom's Taxonomy, where the analyst seeks to achieve all the levels of the taxonomy, in the lifecycle of CTI:
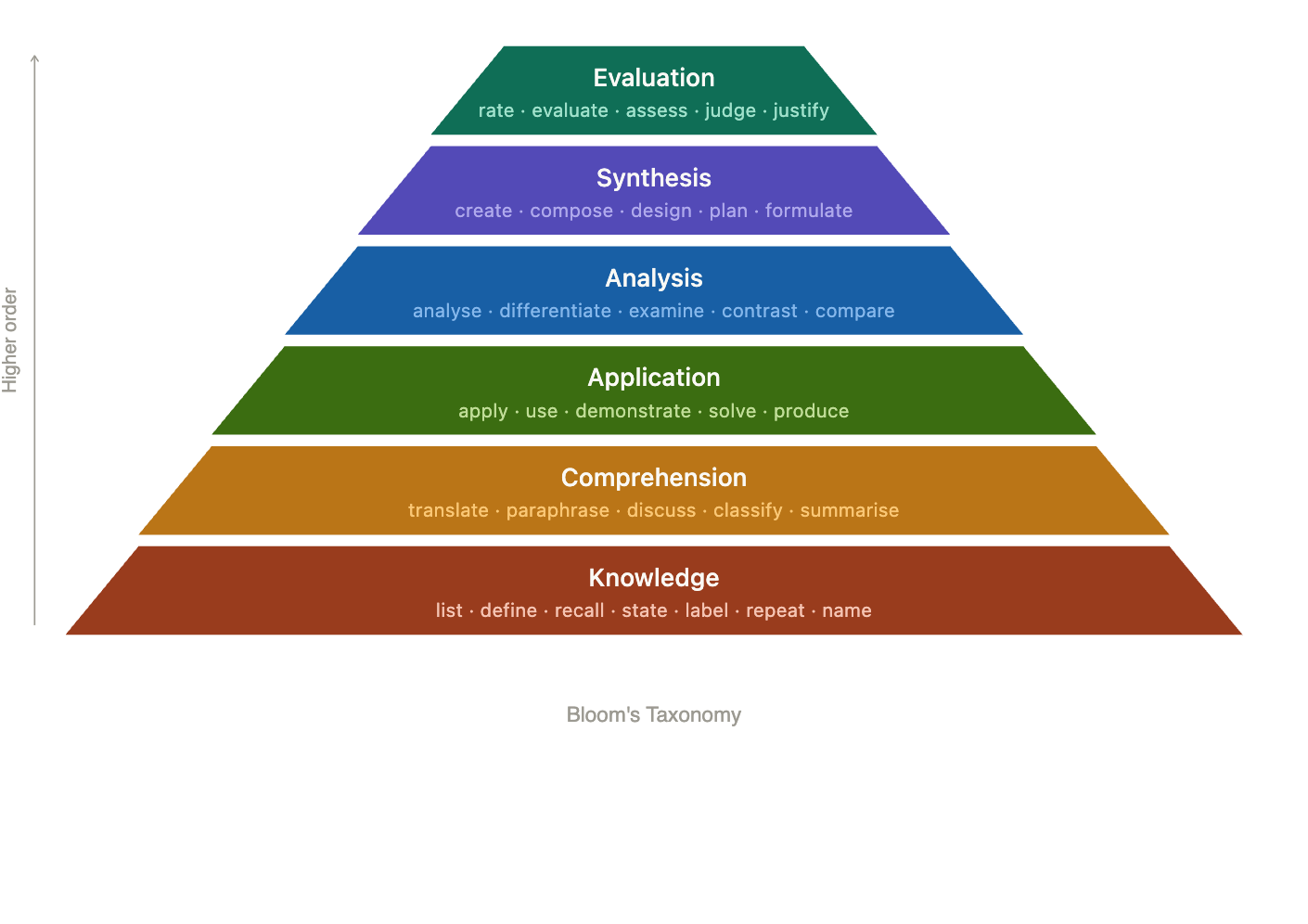
Notice how a data driven hypothesis based CTI cycle starts with (knowledge), seeking to establish context and understanding (comprehension), to then see where things start to make sense for the attack, actor, means and motives, etc, (application), in the (analysis) of all available log data and findings, to then (synthesize) and correlate, to (evaluate) and make a critical thinking decision.
What Do We Really Mean - for SOC/CSIRT/Security Staff?
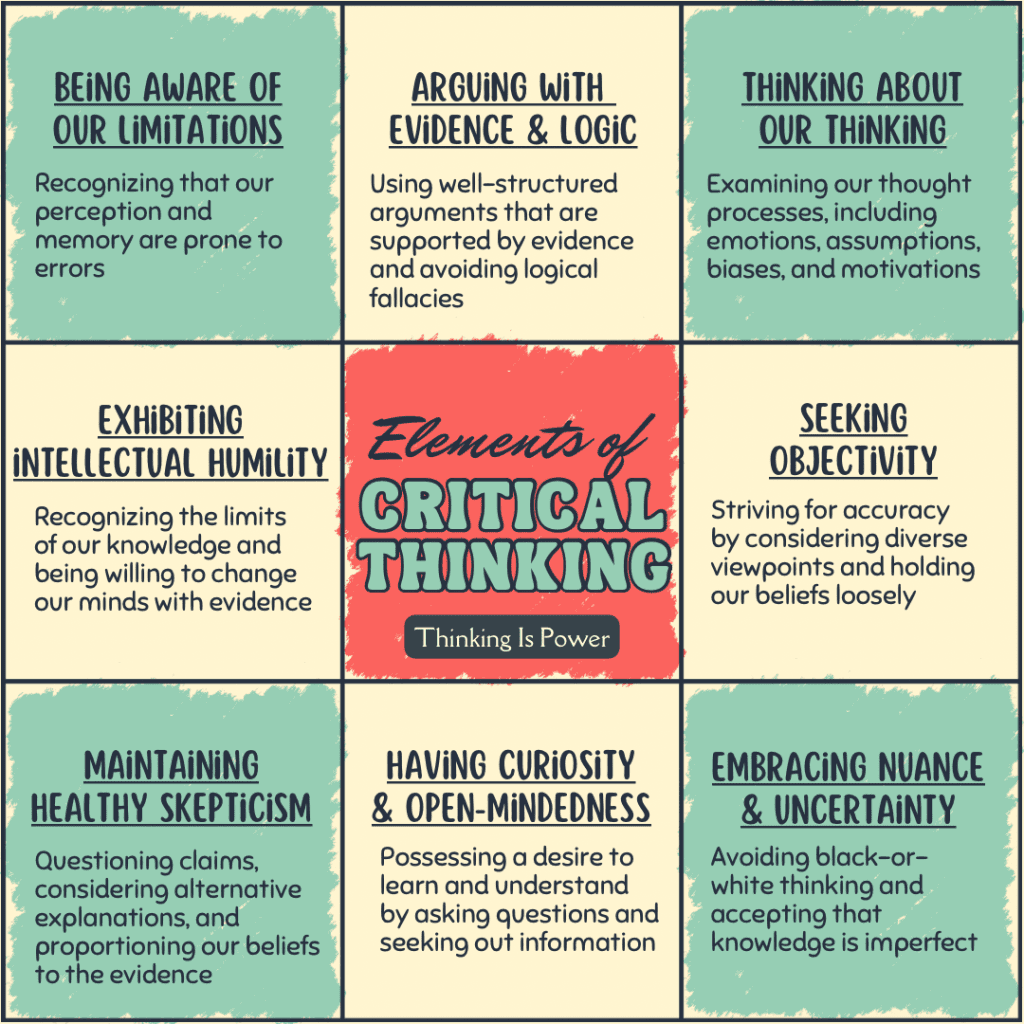
An excellent article on the subject, by Melanie Trecek-King, published at skepticalinquirer.org includes the following image of key ingredients of Critical Thinking:
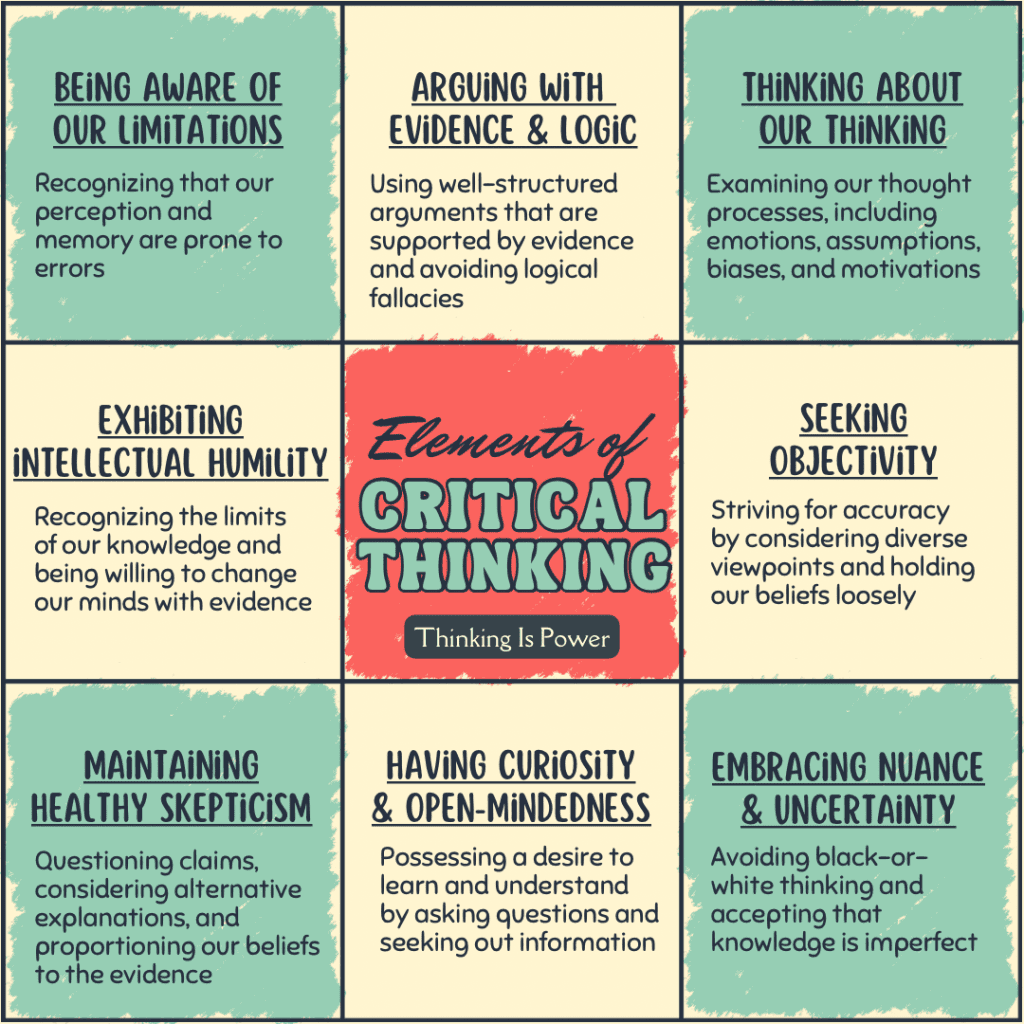
https://skepticalinquirer.org/2024/10/thinking-critically-about-critical-thinking-what-do-we-really-mean/
Notice that the analyst who is performing critical thinking is performing extreme objectivity and intellectual humility to be open-minded and committed to creativity, the unexpected, unknown, and truth beyond bias and assumption.
For example, we see a successful login from a foreign IP address. Is it an attack? Is it a legitimate user from a VPN? What is the reputation of this IP address? What was the activity after login? etc.
Conclusion
Critical Thinking is a process that is supported throughout the entire lifecycle of CTI. It is hypothesis based, just like the analysis process of CTI, and data driven. All levels of thinking (Bloom's Taxonomy) are employed as an analyst considers plausible hypotheses to explain data, information, and findings in establishing context to prove or disprove theories in research and response. Self-Reflection regulation (metacognition) are the essential ingredient of integrity and evaluative outcomes of critical thinking.
Ken Dunham
Graduate of Eastern Oregon University, is a pioneering cybersecurity leader whose career spans from being a middle school teacher and developing early antivirus software to becoming a global CISO-level strategist with extensive counter-threat intelligence experience. His early work included discovering a new class of computer viruses, creating the world's top-downloaded Macintosh security software, and publishing a leading book via McGraw-Hill, followed by a period contributing to aerospace innovation on programs like the Predator drone. He continues to innovate and remediate emergent global threats to reduce risk.
https://www.linkedin.com/in/4d5asecurity/
https://4d5asecurity.com/