What is Cyber Threat Hunting?
By Ken Dunham, 4D5A Security
Thursday, March 26th, 2026
As a pioneer in the world of Cyber Threat Intelligence (CTI), I see many technologies, tools, and people attempting to perform “threat hunting”, without a proper understanding or guidance in how to do it effectively within the lifecycle of CTI. Today, many rely upon tools and technology for “good enough” intelligence, while others chase Indicators of Compromise (IoCs), thinking that is threat hunting - it is not. Join me on a journey to understanding what threat hunting is and is not, and the types of hunts one performs to actionably move the needle to lower cyber risk.
What is Cyber Threat Intelligence (CTI)?
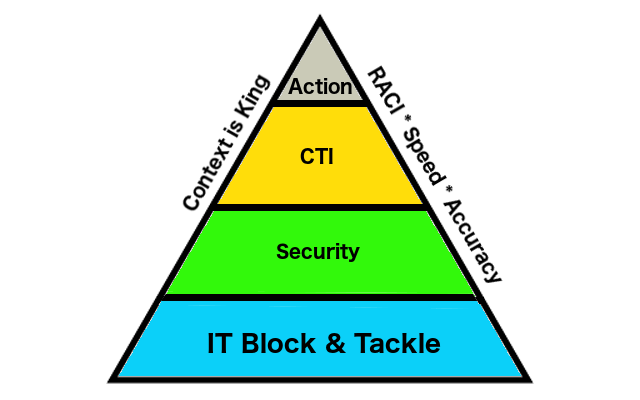
We must start our discussion by understanding the context of what CTI is, where threat hunting occurs:
Cyber Threat Intelligence is the systematic collection, analysis, and dissemination of information pertaining to a company's operation in cyberspace and, to an extent, physical space. It is designed to inform all levels of decision makers.
The analysis is designed to help keep situational awareness about current and arising threats.
Key take-aways of the definition above are the continuous living lifecycle and creation of context to enable actionable outcomes.
What is Threat Hunting?
Threat Hunting is defined as follows:
Threat hunting is a proactive, iterative Cyber Threat Intelligence (CTI) function that aims to reduce the risk to an organization's physical or virtual assets in scope, by assuming compromise, to continually seek unknown or undetected tactics, techniques, and procedures (TTP) or identify threat actors that have gained unauthorized access.
This activity may be structured or unstructured, hypothesis-driven or investigation-based, and require a proactive engagement of the responders.
It is essential that this is a hypothesis driven investigation looking to identify unknown threats and/or actor activities. This is very different from a world of SIEM/SOC/SOAR and Incident Response (IR), where an analyst may find an IOC and attempt to enrich and correlate upon that IOCs (not hypothesis driven).
What is a Hypothesis
A TTPs-driven supposition based upon limited information to further a Cyber Threat Intelligence (CTI) investigation.
e.g. hypothetical hypothesis example below:
Adversaries are concealing TCP port 443, which is not monitored by our organization because it is normally associated with encrypted HTTPS (Hypertext Transfer Protocol Secure) protocol communications.
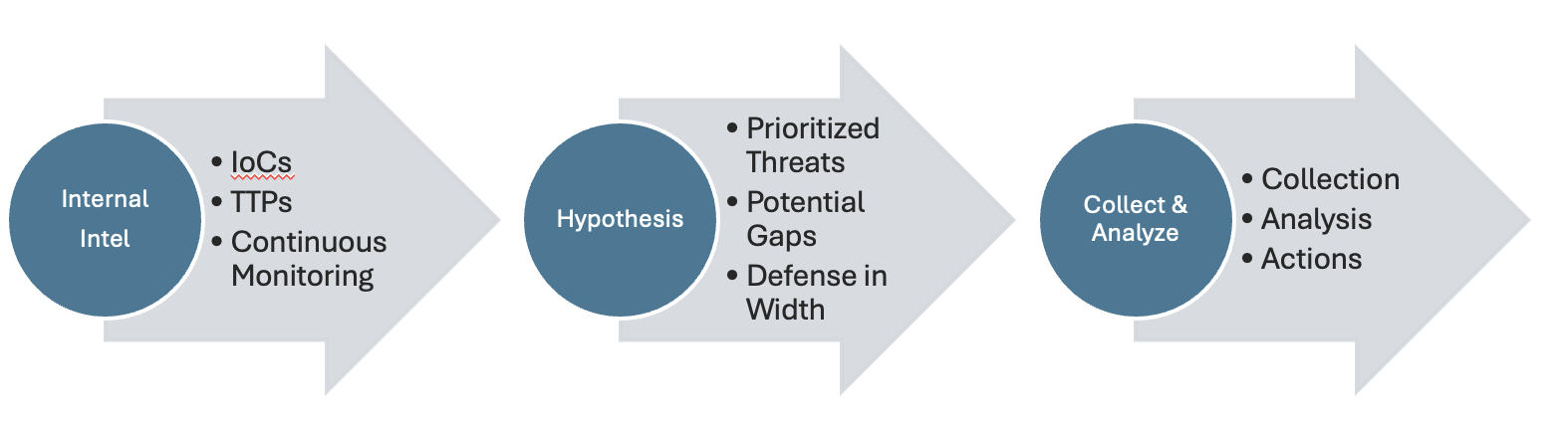
Threat Hunting Process
Threat hunting follows a process of initial internal intelligence, a hypothesis (see the FIRST document on the definition of hypothesis), and collection/analysis,
following standard CTI lifecycle outcomes:
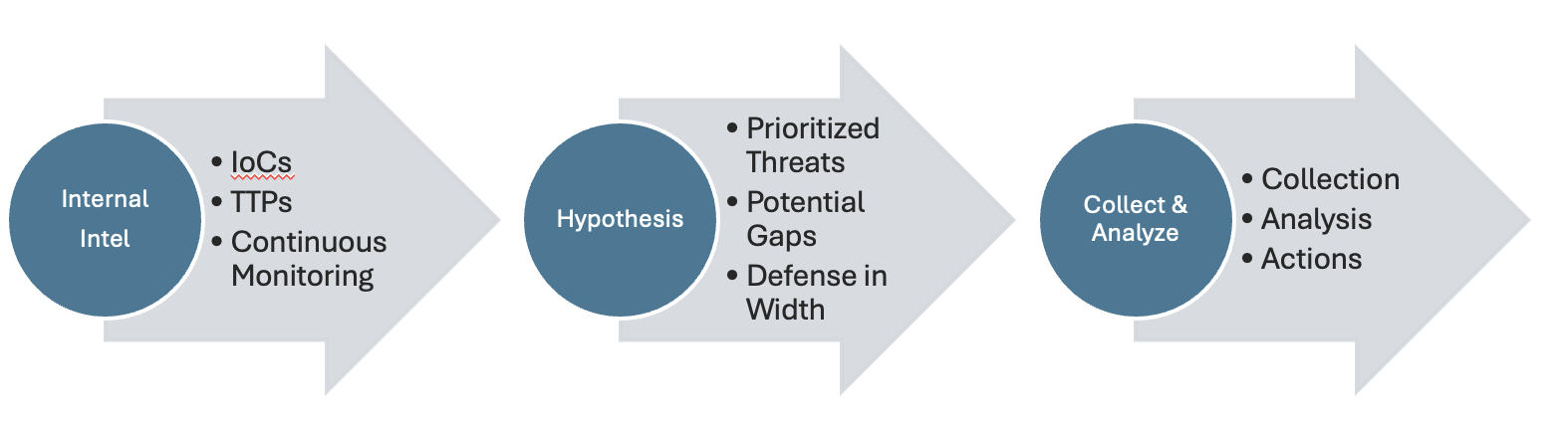
The lifecycle of CTI is evidenced above in three core categories, driven by internal intel, hypothesis for hunting, and the following collection and analysis process. As threat hunting occurs, the analyst determines and evaluates if they are following the right hypothesis or not, in accordance with theory(s) that exist, for their specific prioritized intelligence requirements (PIRs) for threat hunting research and response. The analyst adjusts course, quickly abandoning hypotheses that are proven wrong or improbable, for those that are evidenced as most likely, as the analyst dynamically matures the lifecycle of CTI and threat hunting.
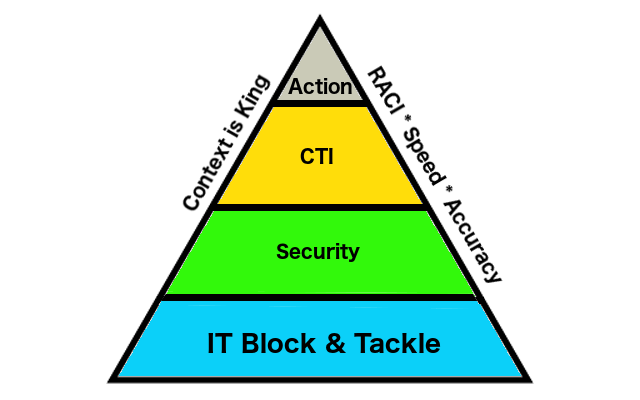
CTI Actionability
Context is created throughout the lifecycle of CTI and threat hunting, eventually leading to actionability. This is the most difficult and important outcome of CTI threat hunting:
"Cyber Threat Intelligence (CTI) Actionability" - Ken Dunham LinkedIn Article
The most important question that an analyst is answering, when performing threat hunting, is related to the question WHY? The analyst must attempt to get to the why behind data, findings, and context as to what is a threat or threat actor attempting to perform, and why; why did a technical event occur at this time and place in this event or incident, etc. Answering WHY establishes context, coupled with a hypothesis-driven way of thinking and doing to support the analytical tradecraft for efficient and effective outcomes.
What is NOT Threat Hunting?
Common challenges related to definitions and employment of threat hunting exist in the wild today, with notables identified below:
- NOT External Indicators of Compromise (IOCs): IOCs are often part of an investigation, but are not the origin; a hypothesis is instead.
8.8.8.8; agent.abc; spam@corporate.com
- Enrichment: Often performed by AI or front-line teams, this is not a core function of threat hunting. It may be included within it, but it does not define it.
Adding context to raw security data, transforming them into observables.
- NOT Dark Web: The focus of threat hunting is upon internal assets and protection. Dark Web queries may be performed as part of that protection, but monitoring Dark Web and going deep here is off the grid for threat hunting. DarkWeb investigations are, however, part of the CTI cycle, but they belong in the “Collection” phase.
- haveIbeenpwnd; Russian Forum; Telegram
- Purple Teaming: Great for demonstrating readiness and maturity, but is not threat hunting. Threat Hunting can be woven into purple team operations to help optimize proactive hardening and reduce risk.
- An excellent way to weave into CTI and threat hunting operations for advanced, mature counterintelligence outcomes
Conclusion
Threat Hunting is designed for your network and assets, where a hypothesis is created and used to quickly create context to proactively reduce risk, blast radius, and implementation of preventative controls to the left of boom.
Ken Dunham
Graduate of Eastern Oregon University, is a pioneering cybersecurity leader whose career spans from being a middle school teacher and developing early antivirus software to becoming a global CISO-level strategist with extensive counter-threat intelligence experience. His early work included discovering a new class of computer viruses, creating the world's top-downloaded Macintosh security software, and publishing a leading book via McGraw-Hill, followed by a period contributing to aerospace innovation on programs like the Predator drone. He continues to innovate and remediate emergent global threats to reduce risk.
https://www.linkedin.com/in/4d5asecurity/
https://4d5asecurity.com/