The world runs on software, and everything is heavily becoming software-defined. Still, we continue to see the vast number of software vulnerabilities and their associated weakness classes leveraged by threat actors/agents. Security-assured software has become vital for all types of software, whether proprietary, free-open-source, commercial-off-the-shelf, and on the operating environment where the software is built. Established best practices are followed to build-in security controls throughout the software development lifecycle. Still, vulnerabilities are discovered and exploited by adversaries to access systems. If we analyze reported security vulnerabilities and correlate them with major attack campaigns, we can see a few patterns emerge in adversaries modus operandi. Specifically, if we review the MITRE ATT&CK framework, which curates adversarial tactics, techniques & procedures (TTPs), and view it through the widely followed software practices and implemented controls, we can harvest valuable insights. This approach can enable organizations to develop the attacker's mindset through documented public domain knowledge. In this talk, we describe a method for extracting optimal practices and specific controls that software development teams can implement to increase resiliency against primary adversarial TTPs. This is achieved by providing a mapping between two foundational frameworks, viz., NIST SSDF (for secure development practices) and OWASP ASVS (security verification standard for web application software and can be generally extended to other types of software). Insights obtained by mapping between ATT&CK mitigations and SSDF/ASVS help select optimal control verification requirements and can provide increased resiliency to software design, development, and deployment. This can be an impactful way to demonstrate how 'Offense' and 'Defense' can complement each other. Software development teams can hugely benefit if the feedback from attack campaigns is fed into secure software development, thereby enabling significant reduction/elimination of weaknesses and vulnerabilities.
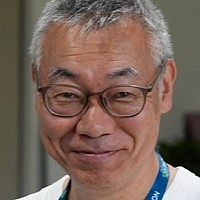
Lokesh Balu currently works with Dell Technologies as technical lead for secure design and development of an 'as-a-service' offer / APEX portfolio. He also leads a program responsible for developing standards and best practices for building 'Trust' controls and requirements into Dell Technologies' as-a-Service offers. His experience includes Secure software development consultancy, Security architecture, Threat modeling, Threat Intelligence, Vulnerability management, Product and Application Security Incidence Response. His prior experience includes security testing enterprise server platforms, systems management software/firmware, and Firewall appliances and service modules. Lokesh has multiple vendor-neutral security certifications from SANS, ISC2, and CSA and has an authorized patent filled with US PTO. He holds a bachelor's degree in Electronics and Communications Engineering and currently pursuing his master's degree in Cybersecurity with IIT Kanpur.