- USTLP:CLEAR
14 Questions Are All You Need
 Carson ZimmermanCarson Zimmerman (Ardalyst, US)
Carson ZimmermanCarson Zimmerman (Ardalyst, US)
Carson Zimmerman has been working in and around security operations centers (SOCs) and CSIRTs for over 20 years. In his current role at Ardalyst, Carson helps clients transform uncertainty into understanding in their digital landscape. In his previous role at Microsoft, Carson led the investigations team responsible for defending the M365 platform and ecosystem. His experiences as a SOC analyst, engineer, architect, and manager led Carson to author Ten Strategies of a World-Class Cybersecurity Operations Center, and co-authored its second edition, Eleven Strategies… which may be downloaded for free at mitre.org/11Strategies.
How is your SOC or CSIRT doing, really? It’s easy to become lost in compliance and regulatory requirements soup. There are plenty of respected consultancies that will perform multi-month SOC assessments. A quick Internet search yields several SOC capability maturity models. And yet, a one-hour conversation with a SOC veteran will yield a gut sense of how a SOC is doing on its journey, and where investments are needed. What if SOCs had a lighter weight method that identifies key strengths and weaknesses: one can be done in an afternoon, or more than twice a year? In this talk, Carson Zimmerman will challenge your thinking about how to measure and drive SOC effectiveness. He will present 14 key indicators of performance, that survey not only how the SOC is doing at a given point of time, but also how well growth and improvement are baked into the SOC culture.
- USTLP:CLEAR
A Recipe for Improving SecOps Detections: Take Three Security Controls, add a Tablespoon of Threat Intelligence, and Let it Rise
 John StonerJohn Stoner (Google Cloud, US)
John StonerJohn Stoner (Google Cloud, US)
John Stoner is a Global Principal Security Strategist at Google Cloud and leverages his experience to improve users' capabilities in Security Operations, Threat Hunting, Incident Response, Detection Engineering and Threat Intelligence. He blogs on threat hunting and security operations and has built multiple APT threat emulations for blue team capture the flag events. John has presented and led workshops at various industry symposia including FIRST (CTI, Tech Colloquium), BSides (SF, Las Vegas), SANS Summits (DFIR, Threat Hunting, Cloud and SIEM), WiCyS, Way West Hacking Fest and DefCon Packet Hacking Village. He also enjoys listening to what his former teammates referred to as "80s sad-timey music."
OK, it’s not that simple, but this talk is designed to identify a prescriptive approach to building detections. Purple teaming, adversary simulation/emulation and automated red teaming are all intended to help defenders to be better prepared. The problem is that these are more initiatives that many of us don’t have the time to undergo with all of the other requirements thrown at us.At the heart of these initiatives is the desire to help organizations build better detections that can handle threats more effectively. Rather than tie ourselves into knots around questions like “is it better to emulate or simulate or run an automated red team”, we need to focus on determining the threats that we need to detect in our environments that align with the actors targeting us.This talk provides attendees with a methodology around testing and validating detections to drive rule development in security operations. Testing cannot take place in a vacuum and should be executed in a representative target environment that includes an organization’s telemetry (EDR/sysmon, NDR/Zeek, for example). We will also examine the role that threat intelligence plays in determining how to prioritize and focus our detection development to the most relevant threats for an organization.This methodology should evolve into an on-going cycle and we will discuss how this ensures rules will continue to function with an added bonus of identifying if data is being ingested and normalized as expected. Finally we will walk through an example that applies this methodology.
- AUTLP:CLEAR
AI Security Bootcamp - A Practical Guide On Securing AI Systems
 Vishal ThakurVishal Thakur (Atlassian, AU)
Vishal ThakurVishal Thakur (Atlassian, AU)
Vishal Thakur has worked in the information security industry for many years in hands-on technical roles, specializing in Incident Response with a heavy focus on Emerging Threats, Malware Analysis and Research. He has presented his research at international conferences (BlackHat, DEFCON, FIRST, SANS DFIR Summit) and has also run training/workshops at BlackHat and FIRST Conference. Vishal is currently working as Senior Director, Cyber Fusion Center at TikTok USDS. In past roles, Vishal worked as a Senior Researcher at Salesforce, helping their Incident Response Centre with advanced threat analysis and developing DFIR tools and has been a part of the Incident Response team at the Commonwealth Bank of Australia. For past few years, Vishal has been involved in ML and AI security and has been researching this subject.
Join our immersive AI Cybersecurity Workshop where participants will learn to build and secure a virtual lab for hands-on practice in protecting AI systems. Delve into the creation of realistic datasets and AI models, essential for simulating cyber threats. Explore the intricacies of injecting anomalies, introducing adversarial attacks, and labeling data for supervised learning scenarios. Gain insights into leveraging pre-existing models, custom model creation, and developing adversarial models for comprehensive security testing. The workshop guides participants in crafting detailed security scenarios, defining use cases, and understanding data flow to simulate real-world AI cybersecurity challenges. Through practical exercises, attendees will master techniques to safeguard AI systems, evaluate defense measures, and hone incident response skills. Elevate your expertise in AI cybersecurity through this dynamic workshop, equipping you to tackle evolving threats in the rapidly advancing landscape of artificial intelligence.
Attendee Training Requirements:
Hardware Requirements:
-
Computer. Participants should have a personal computer or laptop with sufficient processing power and memory to run virtualization software and AI frameworks.
-
Memory (RAM):
A minimum of 8GB RAM is recommended to ensure smooth operation of virtual machines and AI development environments.
-
Storage:
Adequate free storage space to accommodate virtual machines, datasets, and AI models.
-
Processor:
A multicore processor (dual-core or higher) to handle the computational demands of AI model training and virtualization.
Software Requirements:
-
Virtualization Software:
Participants should install virtualization software such as VirtualBox, VMware (preferred), or Hyper-V before the workshop. This will be used to create and manage virtual machines for the lab exercises.
-
AI Frameworks:
Install TensorFlow (instructions will be provided), as well as any other libraries or tools required for model creation and training.
-
Programming Language:
Proficiency in a programming language commonly used in AI development, such as Python, is essential for working with AI frameworks.
-
Security Tools:
Some tools will be required (details and instructions will be provided)
-
Notebook/IDE:
Participants should have a code editor or integrated development environment (IDE) installed for working on AI model scripts and scenarios.
-
Browser:
An up-to-date web browser for accessing online resources, documentation, and collaborative tools used during the workshop.
-
Administrative Access:
Participants may need administrative access to their computers to install and configure software, especially virtualization tools.
-
Document Viewer:
A PDF viewer or document reader for accessing workshop materials, instructions, and resources.
An awareness of network intrusion aiming VPN router vulnerability
Ryosuke Nomoto (Cyber Emergency Center)
Mr. Ryosuke Nomoto was graduated from Kyushu Institute ofTechnology (Iizuka, Fukuoka) and now is working in Cyber Emergency Center, Forensics/Log analyst at LAC/LACERT team. He is focusing his research into on-going intrusion for systems he monitored in ASPAC area.
Since pandemic era where VPN becomes more in usage, it has been monitored intrusion activities into VPN Router system exploited a specific vulnerability, allowing the attacker to gain root privileges by rewriting the system files to tamper the VPN access to conduct further malicious operation.This presentation is a model to understand such threat that is condensed with information explaining the " how, whom, when and what for" such exploitation has been conducted, for all of us to learn the better way to mitigate such incident to happen in the future.
An awareness of network intrusion aiming VPN router vulnerability
September 16, 2024 09:00-09:30
- TW
Attacks On Infrastructure During Cyber Conflicts
 Fyodor YarochkinFyodor Yarochkin (Trend Micro, TW)
Fyodor YarochkinFyodor Yarochkin (Trend Micro, TW)
Fyodor Yarochkin is a Senior Researcher, Forward-Looking Threat Research Senior at Trend Micro with a Ph.D. from EE, National Taiwan University. An early Snort Developer and Open Source Evangelist as well as a Programmer, his professional experience includes several years as a threat investigator and over eight years as an Information Security Analyst.
This presentation is for FIRST Members only, authentication is required on FIRST Portal to preview the video.
Attacks On Infrastructure During Cyber Conflicts
February 16, 2024 11:30-17:00
- DETLP:CLEAR
 Michael SchuelerMichael Schueler (Cisco, DE)
Michael SchuelerMichael Schueler (Cisco, DE)
It is well-known that the team behind the US National Vulnerability Database (NVD) reviews vendor security advisories to confirm or - if deemed necessary - re-score product security vulnerabilities.
Based on feedback the Cisco PSIRT received via the NVD CVMAP Program, we compared the NVD scores to our PSIRT calculated scores for 80 security vulnerabilities Cisco disclosed between May and November 2023. We identified a set of reasons why NVD's and our PSIRT's scores could differ.
This talk will discuss the differences we found, the causes of those discrepancies, and the actions Cisco is taking to ensure NVD's and our PSIRT's scores are better aligned - so our common customers will benefit from the most consistent and accurate scores upon which to base their security risk and vulnerability management decisions.
Michael Schueler is a senior Incident Manager at Cisco's Product Security Incident Response Team (PSIRT). With over 16 years of industry experience, he currently focuses on vulnerability management and disclosure and Cisco products forensic. Prior to this he was working as a Customer Support Engineer at the Cisco EMEA TAC solving highly complex customer issues in technologies ranging from firewalls, VPN, and IDS/IPS over load-balancing and WAN optimization to data center switching. Michael holds a M.Sc. level degree in computer science (Dipl.-Inform.) from RWTH Aachen University, Germany. He is also CCIE Security #23835, CISSP #685496, and GCIH.
- PLTLP:CLEAR
Blueprint for Maturity: Crafting a Tailored Cyber Threat Intelligence Maturity Model
 Kiraga SlawekKiraga Slawek (Standard Chartered Bank, PL)
Kiraga SlawekKiraga Slawek (Standard Chartered Bank, PL)
Working in various intelligence organizations has allowed me to understand the multitude of factors that influence the final production of intelligence satisfying customer needs. However, are all of them equally important? Which ones should we select and focus on when starting our Cyber Threat Intelligence (CTI) program from scratch? Given the abundance of factors, how can we structure them into an achievable action plan that will enable us to build intelligence optimally aligned with our stakeholders' needs?
For the last 15 years, I’ve worked in the world of intelligence. Thanks to being in different roles as an intelligence collector, intelligence analyst, and program or team leader, I’ve had a chance to understand different aspects of CTI. Being responsible for the design and delivery of intelligence products for various kinds of customers (from governmental to corporate), gave me a unique chance to integrate cyber threat intelligence efforts with customers’ needs in different organizations and cultures.
- USTLP:CLEAR
Building a Better Database: How GitHub Structures Their Advisory Database to Drive Developer Outcomes
 Jon MoroneyJon Moroney (GitHub, US)
Jon MoroneyJon Moroney (GitHub, US)
Great effort is often expended managing vulnerability disclosure, from ensuring disclosure is done responsibly to coordinating with software maintainers. Less effort has been spent ensuring that advisories make it to the parties actually using the vulnerable software. At GitHub, we maintain a database with the primary goal of enabling automated vulnerability alerting and remediation tools like Dependabot. We structure our database such that all advisories clearly apply to software that developers use, and we make it easy to get advisories delivered with high precision. The maintenance of the GitHub advisory database reduces noise in developer workflows and enables better experiences that result in more secure software. Come join to hear about tradeoffs, design goals, key insights, and about how GitHub thinks about the pipeline from advisory publication to alert consumption.
Jon Moroney (darakian) is a security analyst at GitHub working in the Security Lab. He is primarily concerned with designing and maintaining the advisory database with the goal that GitHub users have the best experience possible with security alerts.
- USTLP:CLEAR
Building up a PSIRT Team for an Open Source Project: Lessons Learned from Zephyr
 Kate StewartKate Stewart (Linux Foundation, US)
Kate StewartKate Stewart (Linux Foundation, US)
Kate Stewart works with the safety, security and license compliance communities to advance the adoption of best practices into embedded open source projects. Kate was one of the founders of SPDX, and is currently one of the technical working group leads. She is also the co-lead for the CISA SBOM tooling working group, and the OpenSSF SBOM everywhere SIG. Since joining The Linux Foundation, she has launched the ELISA and Zephyr Projects, as well as supporting other embedded projects. With over 30 years of experience in the software industry, she has held a variety of roles and worked as a developer in Canada, Australia, and the US. For the last 20 years has worked with software development teams in the US, Canada, UK, India, and China contributing upstream to opensource.
When the Zephyr project (https://zephyrproject.org/) launched in 2016, one of the goals was to apply known security best practices to make the S in IoT actually mean something. This talk will go through the journey of the last 8 years of applying known best security practices to an open source project, including becoming a CVE Numbering Authority, and forming a PSIRT team from volunteers from different companies. Along the way we had to adjust embargo policies due to a bulk vulnerability report, in addition to the occasional vulnerability reported from the community.
- INTLP:CLEAR
CNA Challenges From a National CERT Perspective
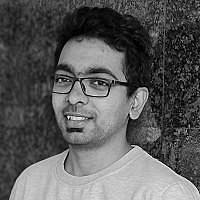
 Mohd. Akram Khan
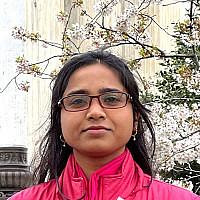
Mohd. Akram Khan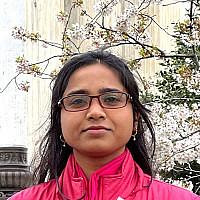 Seema KhanumMohd. Akram Khan (CERT.IN, IN), Seema Khanum (CERT.IN, IN)
Seema KhanumMohd. Akram Khan (CERT.IN, IN), Seema Khanum (CERT.IN, IN)
Indian Computer Emergency Response Team (CERT-In) is the national agency for
responding to cyber security incidents in India. CERT-In is also an authorized CVE
Numbering Authority (CNA) to assign CVE IDs to vulnerabilities under the CVE program. CERT-In carries out responsible vulnerability disclosure and coordination activity for vulnerabilities reported in accordance to the CERT-In’s Responsible Vulnerability Disclosure and Coordination policy. This presentation will provide insights on the challenges faced by CERT-In, operating as both a CVE Numbering Authority (CNA) and as a National Computer Emergency Response Team (CERT).
The presentation will throw light on the challenges in taking responsible decisions
as a National CERT and also as a CNA by taking all potential adverse impacts into account. The dual role requires constant coordination with vulnerability reporters, urging patience and allowing sufficient time for affected entities to patch vulnerabilities. The advantages of a national CERT being a CNA can help in expedited dissemination of vulnerabilities to all the stakeholders. This presentation explores the intricate coordination required between National CERTs, researchers, and OEMs to effectively manage and disclose vulnerabilities in a coordinated manner.
The risk of premature public disclosure by researchers, particularly when OEMs or vendors are unresponsive or exhibit delayed responses, poses a significant concern. Additionally, the reluctance of OEMs/vendors to confirm vulnerabilities, often influenced by National CERT's national stature, further complicates matters. The presentation will also touch upon the criticisms, strategic implications that a national CERT can face due to some decisions.
Mohd Akram Khan has over 16 years of experience at the national Computer Emergency Response Team of India (CERT-In). He currently oversees Responsible Vulnerability Coordination and CVE Numbering Authority activities at CERT-In. His area of expertise spans incident response, threat and breach investigation, insider threat management, cybersecurity situational awareness, security operations centre and responsible vulnerability coordination. He commits himself to support and provide diligent and competent cyber security services to the entire constituency of CERT-In.
Seema Khanum is a valued member of the Coordinated Vulnerability Disclosure (CVD) team at CERT-In and an
active participant in CNA/CVE activities. Her extensive background includes expertise in cybersecurity incident response, network security, and vulnerability exploitation. Seema’s primary focus lies in vulnerability coordination, and she is keen on devising effective mechanisms for coordinating OEMs and researchers in vulnerability disclosure and management. Additionally, she has delivered numerous technical lectures on various cybersecurity topics at awareness programs to organised to promote cyber awareness among women.
- AUTLP:CLEAR
 Dave MatthewsDave Matthews (Gen Digital, AU)
Dave MatthewsDave Matthews (Gen Digital, AU)
After getting his PhD in Mathematics, Dave spent the next 25 years consulting for the Australian Government, primarily working with Defence, Intel and Law Enforcement, before moving to CrowdStrike, and Gen Digital (which is formed from the merger of Avira, Avast and NortonLifelock). He has continually worked in Incident Response and Forensics and has had the privilege of helping people while they are having their worst days at work. He has experience with all flavours of cybersecurity - ranging from attack and defence to incident response as well as security capability development. He is particularly passionate about digital forensics and incident response, helping people prevent and recover from attacks.When he's not working or learning something new, Dave loves spending time with his family and their puppy, Rufus!
This presentation, 'Collaboratively Caring and Securely Sharing', describes situations where sharing Intel would greatly help others. The talk initially discusses forms of Intelligence that are valuable and worth promptly communicating. Examples of how this lack of sharing prevents rapid response to incidents and, in many cases, allows threat actors time to achieve their objectives.Common reasons that prevent sharing are discussed to highlight problems and to show how secure collaboration can help. For example, your organisation might have suffered a breach; you want to share pertinent lessons learned and even Intelligence to help others. However, doing so could expose your reputation. What can you do?Or your organisation might be attacked, and you want to ask for help - anonymously, without divulging where you work.We show how Intel sharing can be achieved in an Incident Responder community and provide step-by-step instructions on implementing with popular team messaging platforms like Slack, Mattermost, Discord and Microsoft Teams. The presentation will demonstrate how this can work in a trusted IR community like FIRST, other CERTs or Incident Response communities.
- USTLP:CLEAR
 Peter AllorPeter Allor (Red Hat, US), Josh Dembling (Intel, US)
Peter AllorPeter Allor (Red Hat, US), Josh Dembling (Intel, US)
Peter Allor is the Senior Director, Product Security for Red Hat. He is been instrumental in Red Hat’s secure development and incident response programs Red Hat and in upstream security groups such as CVE, CVSS, and PSIRTs. He focuses on developing solutions that integrate the full spectrum of security operations within an organizations domain in support of business.
Prior roles include Senior Director for security at Honeywell, Cybersecurity Strategist at BIM and managing vulnerability and incident coordination at IBM for the IBM X-Force. Prior to IBM acquiring Internet Security Systems (ISS), Peter was the Special Assistant to the CEO of ISS for working National Infrastructure Advisory Council (NIAC) problem sets and assisted in forming the Information Technology - Sector Coordinating Council (IT-SCC) where he recently returned to the Executive Committee and Treasurer. As the former Operations Center Director, he ran the Information Technology - Information Sharing & Analysis Center (IT-ISAC) operations and brought coordination across the sector ISACs.
Peter is a Member of the CVE Board, a former member Board of Director of the Forum of Incident Response and Security Teams (FIRST) and its Chief Financial Officer for FIRST. Peter was President to the Industry Consortium for Advancement of Security on the Internet (ICASI) and an Executive Committee Member of the IT Sector Coordinating Council (IT-SCC). A former Commissioner for the CSIS Cybersecurity Commission for the 44th Presidency, he assisted in developing recommendations for the Public and Private Sectors to work collaboratively on Cyber Security.
Peter is a retired Lieutenant Colonel from the US Army. He has Masters Degree from the University of Phoenix, a BS in Business Administration from Rollins College and is a Graduate of the US Army Command & General Staff College.
- NL LU
CoreTIDE: the First Project of the OpenTIDE Family
 Amine Besson
Amine Besson Claus Houmann
Claus Houmann Rémi SéguyAmine Besson (European Commission CSOC, NL), Claus Houmann (Behemoth Cyberdefence, LU), Rémi Séguy (European Commission CSOC, LU)
Rémi SéguyAmine Besson (European Commission CSOC, NL), Claus Houmann (Behemoth Cyberdefence, LU), Rémi Séguy (European Commission CSOC, LU)
Amine Besson is a private contractor focused on designing and engineering large scalable detection systems for his clients, with a track record of innovative solutions deployed in critical sectors and challenging environments.
Claus Houmann is a curator of all things cyber, collecting news for his ever growing library as soon as blog posts get written.
Remi Seguy has worked in cybersecurity for more than 15 years mainly in Blue teams but is most interested to foster purple teaming. Remi fully supports Libre software and tries to contribute to the open source community.
This session will be moderated by: Nikolas Dobiasch (AT)
- USTLP:CLEAR
CSAF/VEX: Improved Security Data
 Martin PrpicMartin Prpic (Red Hat, US)
Martin PrpicMartin Prpic (Red Hat, US)
Security data is a central source of truth for Red Hat customer / consumers as a definitive product guide regarding published, known vulnerabilities and exploits. The availability of accurate information in security data can help provide the correct risk assessment process in customers' vulnerability management programs, which further helps with vulnerability patching prioritization.
In this talk we will focus on both technical and non-technical aspects of vulnerability management based on the new Red Hat Product Security data, and correlation to the Red Hat official SBOMs for Red Hat’s products. We will also discuss how CSAF and VEX data is used within SDL (Security Development Lifecycle) practices. During this session we also show implications of using incorrect security data and consequences visible in the security scanning results.
Key topics to be covered in this session include:
- Why is publishing machine-readable security metadata so important?
- Why CSAF and VEX?
- Red Hat's CSAF/VEX implementation
- CSAF/VEX data and products support model correlation
- Benefits of the relationship between CSAF/VEX and SBOM
- How CSAF/VEX data is correlated to the SDL phase and whole product lifecycle
- Challenges and future improvements
This talk is designed for PSIRT members and all security professionals who work on the vulnerability management processes.
Martin Prpic is a Principal Security Engineer at Red Hat. He is an active participant in the CVE Project's Automation Working Group, the CSAF Technical Committee, and the OpenEoX Technical Committee. Martin's main focus is on designing systems that enable automated vulnerability response, support publishing of accurate security data, and improve the security posture of software supply chains.
VulnCon-CSAF-VEX.pdf
MD5: 1bcf7126d06ce472c851331ae34069a7
Format: application/pdf
Last Update: June 7th, 2024
Size: 687.13 Kb
- USTLP:CLEAR
CVSS SIG Past, Present & Future + CVSS v4.0 Beyond the Numbers: Improving Qualitative Aspects of Vulnerability Disclosure
 Nick LealiNick Leali (Cisco and CVSS SIG Chair, US)
Nick LealiNick Leali (Cisco and CVSS SIG Chair, US)
CVSS SIG Past, Present & Future:
With the recent release of the CVSS v4.0 standard, there continues to be a lot of activity in the FIRST CVSS SIG. This presentation gives an overview of the recent CVSS SIG past, our present ongoing work, and future considerations for CVSS. Attendees are encouraged to come with questions and feedback about their own organizations' use of CVSS, and how the standard and the accompanying documentation can be improved for use by everyone in the vulnerability management community.
CVSS v4.0 Beyond the Numbers:
CVSS numeric scores are simple and lack context helpful to guide vulnerability management. Sometimes we should care twice as much about a 5 than a 10!
This presentation features a discussion of new aspects of the CVSS v4.0 standard that give context to the resulting score, including: supplemental metrics, new to CVSS version 4.0, that provide additional details to describe a vulnerability without changes to the numeric score; the reconfigured vulnerable and subsequent system vulnerability impact metrics help to give increased granular impact ratings; and other new and changed metrics that give greater detail to each assessment. Examples of how score providers and consumers can use these new metrics will be included along the way.
Nick Leali works as an Incident Manager with Cisco PSIRT and serves on the FIRST CVSS SIG, most recently working on the CVSS v4 Examples document.
- US
Cybersecurity Legalities: Mastering Effective Breach Response Strategies
Matt Frontz (Polsinelli PC, US)
Matt Frontz is a Shareholder with Polsinelli PC, an AM100 Law Firm. Originally, a software engineer, he focuses he legal practice on Intellectual Property and related fields.
This session will be moderated by: Joe Tallet (UK)
Digital First Responders: The Role of Computer Security Incident Response Teams (CSIRTS) in Developing Countries
This note intends to provide policy makers in developing countries with a clear understanding of the role and importance of Computer Security Incident Response Teams (CSIRTs) for enhancing cyber resilience. It provides new data and evidence on the status of CSIRT deployment across regions and income groups and outlines practical recommendations on how to establish and operate national CSIRTs, including for costs and staffing.
Built in Partnership with World Bank, read full publication details
- KRTLP:CLEAR
Dissecting the Arsenal of LockBit
 HuiSeong YangHuiSeong Yang (S2W inc., KR)
HuiSeong YangHuiSeong Yang (S2W inc., KR)
HuiSeong Yang is a researcher in the Threat Analysis Team at S2W in Korea. He is in charge of analyzing various malware, including ransomware, and has recently been working on methodologies to analyze malware written in Go and Rust languages, which are often used to make analysis more difficult. His main research focuses on tracking ransomware groups operating as Ransomware-as-a-Service (RaaS).
While many RaaS groups have come and gone in recent years, the LockBit group has been one of the most active. LockBit operates as a ransomware-as-a-service (RaaS) and employs multiple affiliates, causing far more damage than any other ransomware group. As of 2023, it has inflicted 1,029 ransomware victims out of a total of 4,951 ransomware victims, and is aggressive enough to rank first in the number of victims among RaaS groups, at about 20%.the LockBit group has continued to grow their arsenal (which they refer to as a collection): LockBit Red, a 2.0 version of the original LockBit ransomware they developed in June 2021; LockBit Black, which cribbed code from the BlackMatter ransomware in June 2022; and the Conti-based LockBit Green, released this year... How far is the group willing to go to quote code from other ransomware? And then there's the rumored Babuk. As you can see, we've been tracking the LockBit group since its inception.
- JPTLP:GREEN
Email Breach Analysis and Response Tips to Avoid Risk
 Yumi IidaYumi Iida (ITOCHU Cyber & Intelligence Inc., JP)
Yumi IidaYumi Iida (ITOCHU Cyber & Intelligence Inc., JP)
After working as a customer engineer in the authentication and security field at an IT vendor, I am currently in charge of responding to and analyzing security incidents at ITOCHU Cyber & Intelligence.
Business Email Compromise (BEC) poses a global threat, leading to substantial financial losses. Despite the widespread adoption of multi-factor authentication (MFA), attackers have evolved their tactics, notably through Adversary-in-the-Middle (AiTM) attacks, increasingly prevalent since 2021. The Anti-Phishing Working Group (APWG) reports a doubling of phishing attacks between 2020 and 2022, indicating a persistent rise in BEC phishing.Microsoft 365 (M365), the world's most utilized webmail service, is a prime target for these attacks. However, available information on M365 account breaches lacks detailed insights into attackers' behaviors and intrusion trace deletion. The absence of comprehensive incident data hampers effective analysis and monitoring by company CERT (Computer Emergency Response Team).Current defense recommendations, scattered across various documents for different products (Microsoft Entra ID, Exchange, etc.), are not systematically organized. This complicates the work of CERT staff in investigating and responding to incident-related logs. Inadequate incident data may lead to ineffective responses, allowing intrusion risks to persist and potentially amplify damages.This presentation addresses the identified attacker techniques (email theft, app installation, and intrusion trace deletion) from actual M365 account breaches, offering insights for confirmation and response in case of incidents. Through real incident analyses, practical steps for incident handling will be shared to minimize the risk of account compromise and subsequent damage expansion.The goal is to enhance on-site staff response efficiency, disseminate appropriate countermeasures against intrusions and BEC risks, and ultimately contribute to safeguarding numerous companies.
EMAILB-1.PDF
MD5: d41d8cd98f00b204e9800998ecf8427e
Format: application/pdf
Last Update: July 10th, 2024
Size: 6 Kb
- LU BE BRTLP:CLEAR
Empowering Cybersecurity Outreach and Learning through Collaborative Challenge Building, Sharing, and Execution
 Alexandre Dulaunoy
Alexandre Dulaunoy David Durvaux
David Durvaux Renato Otranto Jr.Alexandre Dulaunoy (CIRCL.lu, LU), David Durvaux (European Commission - EC Cybersecurity Operations Centre, BE), Renato Otranto Jr. (CERT.br / NIC.br, BR)
Renato Otranto Jr.Alexandre Dulaunoy (CIRCL.lu, LU), David Durvaux (European Commission - EC Cybersecurity Operations Centre, BE), Renato Otranto Jr. (CERT.br / NIC.br, BR)
Alexandre Dulaunoy enjoys when humans are using machines in unexpected ways.
I break stuff and I do stuff at CIRCL
David Durvaux is active in the incident response field for more than a decade. He has work on many IT security incidents and especially on computer forensics aspects. Since 2015 he is actively preparing the FIRST CTF. David presented several time at the FIRST annual conference among others.
Renato Otranto Jr. is in IT area for more than 25 years and he has experience with security, network and system administration.
He joined CERT.br in 2013 as an incident handler and also develop other activities with the team. Since 2012 he is involved in
the organization of the Capture the Flag at FIRST Annual Conferences. He is also a former member the of Dragon Research Group.
In the dynamic landscape of cybersecurity, continuous skill development is paramount. This presentation, titled "Empowering Cybersecurity Outreach and Learning through Collaborative Challenge Building, Sharing, and Execution," delves into innovative approaches to enhance outreach and learning in the field.Focused on the creation, sharing, and execution of challenges, particularly through platforms like Capture The Flag (CTF), the session aims to illustrate the transformative impact of hands-on experiences with the FIRST.org challenges.The discussion will also outline how it has grown, offering a wide variety of knowledge fields and strong collaboration between the volunteers and their supporting organization.
- TLP:AMBER
Everyday work with OSINT and Telegram
Philippe Lin (Senior Threat Researcher)
Philippe Lin is a senior threat researcher with Trend Micro. He was into big data analysis, machine learning, NLP, SDR and all sorts of nerdy things.
In this talk Phillipe shares how to setup Telegram in a Docker container and automate channel scraping.
This presentation is for FIRST Members only, authentication is required on FIRST Portal to preview the video.
Everyday work with OSINT and Telegram
September 16, 2024 09:30-10:00
- DETLP:CLEAR
Finding, Managing, Preventing Vulnerabilities: An Automotive Perspective (presentation features virtual speakers)
 Andreas Weichslgartner
Andreas Weichslgartner Joyabrata Ghosh
Joyabrata Ghosh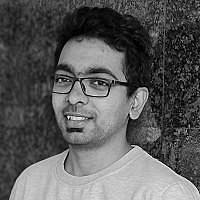 Vineeth BharadwajAndreas Weichslgartner (CARIAD SE, DE), Joyabrata Ghosh (CARIAD SE, DE), Vineeth Bharadwaj (CARIAD SE, DE)
Vineeth BharadwajAndreas Weichslgartner (CARIAD SE, DE), Joyabrata Ghosh (CARIAD SE, DE), Vineeth Bharadwaj (CARIAD SE, DE)
As the automotive industry undergoes a paradigm shift towards software-defined vehicles, the imperative for robust software security becomes obvious. This talk explores the nuanced landscape of identifying, managing, and preventing vulnerabilities from the perspective of an OEM software company.
Starting with an exploration of the escalating role of software in modern vehicles, the talk illuminates the complex software ecosystems that underpin contemporary automobiles. A thorough analysis follows, unraveling the primary sources of vulnerabilities and their potential ramifications on vehicle safety and security.
Central to the discussion is the challenge of handling vulnerabilities within the complex supply chains inherent to the automotive industry. The talk elucidates the difficulties in navigating this multifaceted network of suppliers, emphasizing the necessity for collaborative approaches and effective risk management strategies.
We detail best practices for developing automotive software along the software development life cycle along with various regulation requirements. Especially we highlight the significance of SBOMs in fostering transparency and traceability across the supply chain. The talk delves into how SBOMs can fortify cybersecurity measures by providing a comprehensive understanding of the software components integrated into automotive systems.
Looking forward, the presentation anticipates future challenges and outlines viable solutions confronting the automotive industry, including crypto agility and the incorporation of cryptographic bills of materials (CBOMs).
Mr. Andreas Weichslgartner is currently working as a Senior Technical Security Engineer at CARIAD SE in the product security department.
Joining the Volkswagen Group in 2017, he since then has been developing an embedded intrusion detection system, evaluating security testing technologies, managing vulnerabilities, enabling crypto agility, and working with machine learning in the area of security.
Before, he had been a researcher at the Department of Computer Science, Friedrich-Alexander University Erlangen-Nürnberg (FAU), Germany, from 2010 to 2017. He received his diploma degree (Dipl.-Ing.) in Information and Communication Technology and his Ph.D. (Dr.-Ing.) in Computer Science from the FAU, Germany, in 2010 and 2017, respectively.
Mr. Joyabrata Ghosh is presently working as a Connectivity products security owner at CARIAD SE. Before that, he was responsible for security and legal technical manager for the Elektrobit Automotive Linux platform for the series production of several automotive OEMs. He started his automotive journey with Direct HMI development for BMW ID7 platform. Over a decade ago, his development journey began in embedded and telecom security domains across many OEMs. He supports EO-14028 CISA SBOM working groups and contributed publications: Types of SBOM, Minimum Requirements for VEX. He contributes to nvd@nist.gov and cpe_dictionary@nist.gov for open-source triage. He was co-presenter of Cybersecurity Expectations in Automotive World, 2021, in ELISA Linux safety workgroup. Likewise, he is open-source enthusiast. He has Master’s Degree from the Illinois Institute of Technology in Computer Science, a BS in Computer Science from RCCIIT.
Mr. Vineeth Bharadwaj Prasanna is currently working as a Senior Technical Security Engineer at CARIAD SE in the product security department.
Vineeth joined the Volkswagen Group in 2018, as a security engineer for Audi AG. Since 2020, he has been a member of the offensive security team and has also been working on building up the vulnerability management system, end-to-end security engineering for China GB-T homologation project for the new PPE/PPC platform for the new Audi and Porsche cars at CARIAD SE.
Vineeth received his Master’s degree in Simulation Science from RWTH Aachen University in 2019 with special focus on optimization, and artificial intelligence.
- IN CZTLP:CLEAR
From Code to Crime: Exploring Threats in GitHub Codespaces
 Nitesh Surana
Nitesh Surana Jaromir HorejsiNitesh Surana (Trend Micro, IN), Jaromir Horejsi (Trend Micro, CZ)
Jaromir HorejsiNitesh Surana (Trend Micro, IN), Jaromir Horejsi (Trend Micro, CZ)
Nitesh Surana is a Senior Threat Researcher with Trend Micro where he specializes in cloud vulnerability & security research. He has been in the top 100 MSRC Most Valuable Security Researchers in 2023 for his submissions to Microsoft via the Zero Day Initiative. He has presented across conferences such as Black Hat USA, HackInTheBox, HackInParis, Nullcon, c0c0n, Security BSides, NDC Oslo and OWASP/Null Bangalore meetups. Apart from playing with packets and syscalls, Nitesh is found attending concerts and writing/playing music.
Jaromir Horejsi is a Senior Threat Researcher for Trend Micro Research. He specializes in tracking and reverse-engineering threats such as APTs, DDoS botnets, banking Trojans, click fraud, and ransomware that target both Windows and Linux. His work has been presented at RSAC, SAS, Virus Bulletin, HITB, FIRST, AVAR, Botconf, and CARO.
Cloud-based development environments enable developers to work from any device with internet access. Introduced during the GitHub Universe event in November 2022, Codespaces offers a customizable cloud-based IDE, simplifying project development. However, the openness of this service has been exploited by attackers, leading to in-the-wild campaigns leveraging GitHub Codespaces for developing, hosting, and exfiltrating stolen information.The presentation will showcase GitHub Codespaces' features and explore typical methods of abuse by threat actors, focusing on observed malicious campaigns. Highlighted is DeltaStealer, a credential-stealing malware family with diverse variants, some featuring unique capabilities like persistent Discord authentication compromise and cloud-based data exfiltration.Developed using GitHub Codespaces, these infostealers reveal interesting artifacts, including debug symbols, exposing insights into the developers' identities. The presentation will showcase social media evidence and conclude with practical recommendations on configuring cloud-based IDEs securely, identifying suspicious instances, and proactively addressing similar cyber threats.
- ILTLP:CLEAR
From SBOM to VEX - Discovering What's in the Box and How Badly it Can Hurt You
 Ben HirschbergBen Hirschberg (ARMO, IL)
Ben HirschbergBen Hirschberg (ARMO, IL)
Vulnerability Exploitability eXchange (VEX) documents have emerged as a manifest of vulnerabilities of a software product, aligned with the concept of Software Bill of Materials (SBOM), serving as a standardized way for software producers to communicate info about the exploitability of known vulnerabilities within products. The adoption and support of VEX documents represent a major shift in cloud native security, designed to help determine which vulnerabilities require immediate attention & remediation. Yet the widespread adoption of VEX faces a fundamental obstacle--the sourcing of reliable & accurate VEX docs.
Enter the CNCF & OSS projects, that have made significant progress in the generation of reliable VEX documents, by using eBPF technology, which then automatically categorizes vulnerabilities by priority and enables the loading to other popular OSS projects like Trivy or Grype, that support OpenVEX. Come to this session to learn how to get started with VEX immediately.
Ben Hirschberg is a veteran cybersecurity and DevOps professional, as well as computer science lecturer. Today, he is CTO and co-founder at ARMO, with a vision of making end-to-end Kubernetes security simple for everyone, and a core maintainer of the open source Kubescape project. He teaches advanced information security academically in both undergrad and graduate courses. In his previous capacities, he has been a security researcher and architect, pen-tester and lead developer at Cisco, NDS and Siemens.
- US
From Soup to Nuts: Building a Detection-as-Code Pipeline
 David FrenchDavid French (Google Cloud , US)
David FrenchDavid French (Google Cloud , US)
David French is a Detection & Response Engineer and Threat Hunter with many years of experience both working as a defensive cybersecurity practitioner and on the vendor side of life doing threat research and building security solutions. He currently works at Google Cloud where he helps security practitioners defend their organization from attack using Chronicle Security Operations.
This session will be moderated by: Nikolas Dobiasch (AT)
- GBTLP:CLEAR
How to Start Using Priority Intelligence Requirements (PIRs) on a Budget
 Josh Darby MacLellanJosh Darby MacLellan (Feedly, GB)
Josh Darby MacLellanJosh Darby MacLellan (Feedly, GB)
Cyber Threat Intelligence (CTI) professionals are increasingly confronted with pressure to deliver more intelligence services and products with fewer resources. Balancing escalating threats against budget cuts and limited tools stretches CTI teams thin, leading to burnout and high turnover. To provide clarity on priorities, the CTI community adopted Priority Intelligence Requirements (PIRs). PIRs are a pivotal method for refocusing efforts and resources, building relationships between CTI and stakeholders, and enabling greater efficiency. But how does one begin collecting PIRs when there is minimal budget in the first place? How do you approach the first 90 days to ensure you implement PIRs without incurring high costs?
This session takes a pragmatic approach to developing PIRs, complementing previous workshops on PIRs (including at this conference) by focusing on the earlier stages and working with a limited budget.
Josh is a Cyber Threat Intelligence (CTI) professional with experience in the financial, tech, and cybersecurity sectors in North America and Europe. He originally started out in physical threat intelligence and has worked in geopolitical risk, protective intelligence, and risk management before pivoting to the CTI. Josh's current job focuses on using Machine Learning Models to collect cyber threat intelligence.
Josh enjoys contributing to the threat intelligence community and mentoring others in the industry. He sits on the Board of Director for TIER (Threat Intelligence Exchange Roundtable) and on the committee for CyberToronto Conference, previously holding directorships with (ISC)2 Toronto Chapter and ASIS.
- TLP:CLEAR
Improving ICS/OT Threat Hunt & Incident Response Capabilities Through Adversary Emulation
 Shaun LongShaun Long (Cybersecurity & Infrastructure Security Agenc)
Shaun LongShaun Long (Cybersecurity & Infrastructure Security Agenc)
Shaun Long is the Deputy Chief for CISA’s Threat Hunting - Industrial Control System Section (ICSS), with a focus on reducing risk for small-medium sized critical infrastructure partners, building free & open-source community operational technology (OT) cyber tools, and building scalable service offerings using the Control Environment Laboratory Resource (CELR) platform. In addition to enabling internal CISA Threat Hunting teams & established partners, Mr. Long's team prioritizes partnerships with regional critical infrastructure utilities to demystify OT Cyber Security through interactive CELR Threat Hunting exercises, capture the flag events, and technical training modules focused on sector specific challenges.
Prior to joining CISA, Mr. Long spent eight years working at Booz Allen Hamilton -- supporting clients with technical product assessments, security and network architecture assessments, and enterprise level cyber security tool deployments. In addition to client work, Mr. Long helped to stand up an entirely new cross-cutting business unit, targeting the industrial control system security in the Defense & Civilian market by partnering with functional market leaders and leading commercial vendors.
This presentation will delve into the challenges and opportunities involved in upskilling the current workforce and training the future workforce to tackle the emerging field of cybersecurity—cyber-physical systems and operational technology that power our modern world. We will examine how the Cybersecurity & Infrastructure Security Agency (CISA) leverages our Control Environment Laboratory Resource (CELR) to conduct simulated OT threat hunt and incident response exercises. Additionally, we will explore how these systems are used to develop products and services for public and community use, and investigate new use cases and offerings to strengthen critical infrastructure against evolving threat actors.
- PLTLP:CLEAR
Invisible Strings – Contemporary Challenges And Techniques Of Infrastructure Tracking
 Kamil BojarskiKamil Bojarski (Standard Chartered Bank, PL)
Kamil BojarskiKamil Bojarski (Standard Chartered Bank, PL)
Discovery and tracking of adversarial infrastructure are one of the most common tasks of threat intelligence teams and can yield significant insights into adversary operations. However, increasing adoption of cloud services and use of privacy protection have enabled threat actors to blend command-and-control nodes with legitimate hosts that present similar features and profile. The talk aims to discuss challenges related to infrastructure analysis and propose a robust methodology leading to resilient tracking techniques. Using Joe Slowik's concept of treating indicators as composite objects, we will focus on profiling network artifacts like TLS certificates, exposed host services, and domains. By observing and combining multiple characteristics, analysts can establish patterns and signatures representing how an activity group creates their infrastructure, and as such gain more confidence in early detection and attribution.
The presentation will include use cases of tracking post-exploitation frameworks servers and role of infrastructure analysis in activity group clustering. The examples will aim to demonstrate how to fully exploit data that can be derived from an indicator utilizing the author's guide (available at https://bit.ly/infrastructure-exploitation) and data collected from widely accessible services such as Shodan or Censys.
Kamil Bojarski works as a Senior Analyst at Standard Chartered Bank's Client and Third-Party Intelligence team where he tracks down adversarial activity affecting the Bank's supply chain and supports outreach efforts. Kamil is also a teaching assistant at SANS Institute supporting students during FOR578 Cyber Threat Intelligence course, and a member of GIAC Advisory Board. You can read his musings on threat intelligence, OSINT and national security at counterintelligence.pl. His research interests are focused on counterintelligence aspects of information security, activity of eastern APT groups and cross-section of technical and political aspects of cyber operations.
- TWTLP:GREEN
IoT Hacks - Unexpected Angles of Human Process Compromises
 Fyodor YarochkinFyodor Yarochkin (Trend Micro, TW)
Fyodor YarochkinFyodor Yarochkin (Trend Micro, TW)
Dr. Fyodor Yarochkin is a Senior Researcher, Forward-Looking Threat Research Senior at Trend Micro with a Ph.D. from EE, National Taiwan University. An early Snort Developer and Open Source Evangelist as well as a Programmer, his professional experience includes several years as a threat investigator and over eight years as an Information Security Analyst.
Fyodor explores the evolution of tools designed to influence public opinion, focusing on physical devices that can shape perception, such as IoT cameras, vehicle telematics, and various other systems.
This presentation is for FIRST Members only, authentication is required on FIRST Portal to preview the video.
IoT Hacks - Unexpected Angles of Human Process Compromises
November 13, 2024 17:20-18:00
- USTLP:CLEAR
KPIs for CSIRTs
 Logan WilkinsLogan Wilkins (Cisco, US)
Logan WilkinsLogan Wilkins (Cisco, US)
Logan Wilkins has over 25 years of software development and information security experience. He has worked in academic, research, and corporate settings, specializing in DevSecOps management, data science, and information security. In his current role, Logan manages Cisco's CSIRT Engineering Delivery team, which is responsible for Security Monitoring and Incident Response systems development, CI/CD processes, and Data Management. Logan is Co-chair of the FIRST Metrics Special Interest Group (SIG).
In the rapidly evolving landscape of cybersecurity, organizations increasingly rely on effective Cybersecurity Incident Response Teams (CSIRTs) to detect, respond to, and mitigate security incidents. Key Performance Indicators (KPIs) play a crucial role in assessing the efficiency and effectiveness of CSIRT operations. This half-day training class is designed to empower CSIRT professionals with the knowledge and skills to develop, implement, and leverage KPIs for enhanced incident response.
The training will cover essential topics, including:
- Understanding CSIRT Objectives: Participants will gain insights into the core objectives of a CSIRT and how KPIs align with these goals. A comprehensive overview will be provided to establish a foundation for KPI development.
- Identification and Selection of Relevant KPIs: Explore a range of KPIs applicable to CSIRTs, considering factors such as incident detection, response times, and containment effectiveness.
- Metrics and Measurement Techniques: Delve into the methodologies for measuring KPIs accurately. Participants will learn how to define and collect relevant metrics.
- Establishing Baselines and Targets: Understand the significance and pitfall of setting baselines and realistic targets for KPIs. Practical examples and case studies will be discussed to illustrate how organizations can benchmark their CSIRT performance.
- Visualization and Reporting: Learn effective ways to present KPI data through visualizations and reports.
Following this training, participants have additional knowledge and tools to help establish a KPI framework tailored to their CSIRT's objectives. This class provides a opportunity for CSIRT professionals to enhance their skills, optimize their operations, and contribute to the overall security posture of their organizations.
- USTLP:CLEAR
 Krassimir Tzvetanov, PhDKrassimir Tzvetanov, PhD (Purdue University, US)
Krassimir Tzvetanov, PhDKrassimir Tzvetanov, PhD (Purdue University, US)
For the past five years Krassimir Tzvetanov has been a graduate student at Purdue University focusing on Homeland Security, Threat Intelligence, Operational Security and Influence Operations, in the cyber domain.
Before that, Krassimir was a security engineer at a small CDN, where he focused on incident response, investigations and threat research.
Previously he worked for companies like Cisco and A10 focusing on threat research and information exchange, DDoS mitigation, product security.
Before that Krassimir held several operational (SRE) and security positions at companies like Google and Yahoo! And Cisco.
Krassimir is very active in the security research and investigation community and has contributed to FIRST SIGs. He is also a co-founder and ran the BayThreat security conference, and has volunteered in different roles at DefCon, ShmooCon, and DC650.
Krassimir holds Bachelors in Electrical Engineering (Communications), Masters in Digital Forensics and Investigations, and Masters in Homeland security.
Overview: In this presentation the author goes over the building blocks of Influence Operations using mass and social media. It covers subjects such as hypodermic needle model, two-step flow of information, gatekeeping, agenda-setting, priming, framing, spiral of silence, echo chambers and cultivation.
In addition, it looks at some of the larger scale operations focused on subversion.
Additional materials
Media Effects Used in Influence Operations (part 1)
October 17, 2024 09:00-09:50
- IT ESTLP:CLEAR
Nestlé Unified Vulnerability Management Approach
 Angelo Punuriero
Angelo Punuriero Jenifer Jimenez
Jenifer Jimenez Martin KarelAngelo Punuriero (Nestlé, IT), Jenifer Jimenez (Nestlé, ES), Martin Karel (Nestlé, ES)
Martin KarelAngelo Punuriero (Nestlé, IT), Jenifer Jimenez (Nestlé, ES), Martin Karel (Nestlé, ES)
Nestlé and similar organizations encounter numerous challenges in Vulnerability Management. These include managing large and diverse environments, accommodating various technologies with distinct requirements, navigating complex ownership structures, coordinating multiple security teams and tools, and adapting to constant change.
To address these challenges, my team and I have made it our mission to create a comprehensive platform that integrates the most practical approaches for each specific environment. By doing so, we aim to increase automation, enhance situational awareness, and unlock a multitude of use cases and reporting capabilities.
In addition to consolidating results from different traditional vulnerability scanning tools and penetration tests, we recognize the importance of analyzing vulnerabilities that are disclosed by vendors but may not be detected by scanners.
We have implemented a crucial activity that involves automatically categorizing non-critical vulnerabilities and communicating them to the respective patching teams, aligning with their specific patching schedules. For critical vulnerabilities, we have established a more aggressive remediation process.
This process is closely integrated with the scanner findings, which helps to address challenges related to ownership, tracking, and SLA calculations. By linking these components together, we are able to streamline vulnerability management and ensure efficient resolution of identified issues and overall visibility.
Angelo Punturiero is an Italian native who has recently moved to the enchanting city of Barcelona. He proudly serves as a Vulnerability Management Senior Specialist in the Nestle’ CSOC Vulnerability Management team. With a deep passion for cybersecurity and the art of fine cuisine, he has improved he's skills through years of experience at renowned IT consulting firms. This professional journey has led him to Nestle’, where he coordinates the process that determines the Corporate Rating of the daily published CVEs, ensuring that the appropriate stakeholders are promptly informed of any imminent risks. Additionally, he actively engages in matters related to Cloud Security and contributes to projects involving Generative AI in the realm of cybersecurity.
Jenifer Jiménez, native of Spain, is currently working as a Senior Vulnerability Management Specialist at Nestlé Global Services in Barcelona. She is vulnerability management orchestration platform lead architect. Prior to her current role, she was part of the team providing security services to global Hewlett-Packard customers, as well as managing the development of security platforms for the CSIRT at CaixaBank. With a deep passion for her work and a commitment to staying at the forefront of industry trends, she strive to make a positive impact in the field of cybersecurity. Her dedication to securing critical systems and her love for salsa dancing and family bring a unique blend of expertise and personal fulfillment to her life.
Martin Karel, a native of Slovakia, is currently leading the Nestlé global vulnerability management and offensive security team based in Spain. He has been a part of the Global CSOC since its establishment in 2016 and has played a crucial role in various key projects, including incident response, security monitoring, and the centralization and automation of vulnerability management processes. Prior to his current role, Martin led similar projects at HP Enterprise and SEAT, a car manufacturer within the VW group. In his leisure time, he is passionate about ballroom dancing and values spending quality time with his two daughters.
- AT LUTLP:GREEN
NeuroCTI - a Custom Fine-Tuned LLM for CTI - Benchmarking, Successes and Lessons Learned
 Aaron Kaplan
Aaron Kaplan Alexandre Dulaunoy
Alexandre Dulaunoy Jürgen BrandlAaron Kaplan (Independent / EC-DIGIT-CSIRC, AT), Alexandre Dulaunoy (CIRCL.lu, LU), Jürgen Brandl (Federal Ministry of the Interior, Austria, AT)
Jürgen BrandlAaron Kaplan (Independent / EC-DIGIT-CSIRC, AT), Alexandre Dulaunoy (CIRCL.lu, LU), Jürgen Brandl (Federal Ministry of the Interior, Austria, AT)
Aaron is currently working for EC-DIGIT-CSIRC where he focuses on how to leverage the power of Large Language Models (LLMs) for CTI purposes. Prior to joining EC-DIGIT-CSIRC, Aaron was employee #4 of CERT.at. He co-founded intelmq.org.
In the field of AI, Aaron co-founded deep-insights.ai, a medical AI research group focussing on delivering deep learning based classifiers for the rapid detection of lesions in the human body. He also co-chairs the AI Security SIG at FIRST.org. Aaron likes to come up with ideas which have a strong benefit for (digital) society as a whole and which scale up. He loves sharing knowledge and open source tools to automate stuff.
Alexandre Dulaunoy enjoys when humans are using machines in unexpected ways.
I break stuff and I do stuff at CIRCL
Jürgen Brandl is a senior cyber security analyst at the Federal Ministry of the Interior and has 10 years of experience working in incident response, protecting both governmental and critical infrastructure from cyber attacks. In his current role, he is researching and advocating for the need to use AI to face the emerging threat landscape.
Phd. Paolo Di Prodi was a senior data scientist at Microsoft and Fortinet. Since late 2022 he founded a company called Priam Cyber AI ltd that uses virtual agents to automate security operations. He contributes regularly to open source projects from OASIS like STIX2.1,MITRE ATLAS,IOB and various LLM projects such as OLLAMA and LiteLLM. He also a member of the Automation AI SIG in FIRST ORG and contributed to developing EPSS at the RAND ORG.
LLMs turn out to be highly practical for summarising and extracting information from unstructured Cyber Threat Intelligence (CTI) reports. However, most models were not trained specifically for understanding CTI. We will present a custom LLM, fine-tuned for CTI purposes. But of course, that only makes sense with a CTI text benchmark dataset. Creating these two systems is a challenging journey. Set-backs guaranteed. We will share our findings. Comes with batteries and MISP-integration.
- US
Offense v Defense: Digging into GraphRunner and Microsoft Graph API Log Sources You May Not Be Looking At But Should
 Dave Herrald
Dave Herrald John StonerDave Herrald (Google Cloud Security, US), John Stoner (Google Cloud, US)
John StonerDave Herrald (Google Cloud Security, US), John Stoner (Google Cloud, US)
Dave Herrald has over 25 years of experience as a technical security practitioner and leader across many industries, including technology, payments, manufacturing, media, and software. In recent years, Dave’s passion has been to improve the experience of information security analysts by developing large-scale experiential learning programs. Dave co-created Splunk’s Boss of the SOC (BOTS) blue-team CTF, reaching tens of thousands of security professionals globally. Today, Dave leads the Adoption Engineering team at Google Cloud Security, focusing on field research and developing programs for the success of security practitioners. Dave holds a degree in computer science from Iowa State University and has earned many security certifications, including GIAC GSE #79. Dave and his family live in Colorado, where he enjoys skiing, cycling, and woodworking.
John Stoner is a Principal Security Strategist at Google Cloud and leverages his experience to improve users' capabilities in Security Operations, Threat Hunting, Incident Response and Threat Intelligence. He blogs on threat hunting and security operations and has built multiple APT threat emulations for blue team capture the flag events. John has presented and led workshops at various industry symposia including FIRST, BSides, SANS Summits and DefCon Packet Hacking Village. He also enjoys listening to what his former teammates referred to as "80s sad-timey music."
This session will be moderated by: Joe Tallet (UK)
- TT
Operationalizing Threat Intelligence
 Rick Logan-StanfordAnish Bachu (TTCSIRT, TT), Rick Logan-Stanford (TTCSIRT, TT)
Rick Logan-StanfordAnish Bachu (TTCSIRT, TT), Rick Logan-Stanford (TTCSIRT, TT)
Rick Logan-Stanford is a progressive ICT/Security Professional who is fully capable of handling any challenges by engaging the sum of his collective experience and training. Thirteen years of employment has made him proficient in designing, maintaining and troubleshooting Active Directory, MS Exchange and network security. Currently focused on advancing in a career in Cyber Security, building proficiency in, but not limited to, incident response, digital forensics, vulnerability assessments and cyber-related laws.
This session will be moderated by: Gabi Cirlig (UK)
- DETLP:CLEAR
Predictive Cyber Defense - Early Warning Intelligence & Forecasting (08:30-12:30)
 Robin DimyanogluRobin Dimyanoglu (OC Payment GmbH, DE)
Robin DimyanogluRobin Dimyanoglu (OC Payment GmbH, DE)
This workshop introduces Early Warning Intelligence (EWI), a predictive approach that orchestrates cyber defense by anticipating threats before they materialize. Incorporating structured analytical techniques, we will explore two distinct methodologies for constructing an EWI system: profile-driven and correlation-guided research approaches, drawing from practical examples and previously published works.
This workshop will not only dissect these methods but will also argue for the integration of temporary countermeasures—a concept introduced to adjust cyber defense dynamically in response to elevated threat levels. Examples include tweaking rate limits and bot scores, configuring increased resources, and temporarily disabling features to mitigate impact, showcasing a shift from static to adaptive security postures.
Robin Dimyanoglu is the Red Team Lead at HelloFresh Global, with extensive experience in Cyber Threat Intelligence and Threat-Informed Defense. Robin is inspired to bring in concepts from war and intelligence studies to the field of cybersecurity. With a passion for staying ahead of the curve, he is committed to developing novel solutions to security problems.
- AUTLP:CLEAR
Processing Threat Reports at Scale Using AI and ML: Expectations and Reality
Yury Sergeev (RST Cloud Pty Ltd, AU)
With an emphasis on leveraging Artificial Intelligence (AI) and Machine Learning (ML), the session demonstrates an automated approach to streamline the collection, processing, and analysis of threat intelligence reports (APT reports, DFIR reports, malware analysis reports, threat reports, etc.) at scale. The proposed methodology focuses on technical insights, spanning the identification and monitoring of relevant resources, automatic classification using ML to filter out irrelevant information, and the preservation and extraction of valuable threat data with conventional and AI techniques. Attendees will gain insights into optimising their workflows, including the extraction of meaningful information from reports, summarisation techniques, and the automated conversion of reports into the STIX format.
As a cybersecurity expert with a profound understanding of enterprise IT and OT infrastructure, they leverage their expertise to audit, plan, design, develop, and implement complex Information Security systems. Their impressive track record, consisting of over 90 successful cybersecurity projects, consistently enhanced the security of enterprises across multiple countries and industries.
After 6 years working for Deloitte Cyber Intelligence Centre as a security engineer and later as a Director, founded a company called RST Cloud that specialises in Threat Intelligence.
Their focus now centres on operationalisation of threat intelligence, staying vigilant against emerging threats, and guiding teams effectively towards project goals and objectives.
- JPTLP:CLEAR
Pushing Coordinated Vulnerability Disclosure forward in Asia Pacific
 Tomo ItoTomo Ito (JPCERT/CC, JP)
Tomo ItoTomo Ito (JPCERT/CC, JP)
CVD is a global good practice. In today's CVD ecosystem, many different stakeholders exist, but they are largely from the United states or EU. "Asia-Pacific CVD" has not been cultivated. Many software product/component suppliers exist in the region, and the size of the enterprises vary from large to small. In the region, CVD readiness - such as Vulnerability Disclosure Policy preparation or being a CNA - is lacking overall. Also, cooperative structure by the CVD Coordinator organizations has not been built. Realizing such issues and to start tackling them, CVD Working group in the Asia-Pacific's CSIRT community APCERT, was created by the region's several CERT/CVD Coordinator organizations. Referencing precedents such as ENISA setting up a CVD structure in EU, the WG is first starting off with learning each member organization's activity through presentations, and is finding out what the characteristics and specific challenges are in the region.
In this presentation, the WG's motivation, activities, the challenges found so far will be explained. Also, discussions to gather information and opinions from the audiences for the WG to grow to become a good CVD supporter (e.g., topics such as "what would be helpful or what was not by the CVD coordinators in the region", efficient awareness raising methods, etc.,) will be held.
Tomo Ito has been working as a vulnerability information coordinator at JPCERT/CC for 4 years. His current focuses include international collaborations regarding vulnerability coordination topics with organizations around the globe.
- HUTLP:CLEAR
Raising the Effectiveness of Your Threat Management Program
Ememobong Eyo (HU)
Businesses are out to make profit. As they operate and strive for growth, they rely on threat management teams to protect them. But is a focus on industry threats the most effective approach? This session will capture a concept to driving security into security-conscious businesses, what it looks like, and how it compares to conventional threat management practices.
Ememobong Eyo helps organisations operate securely. Having led a threat management team serving multiple global businesses, she believes that more than managing day-to-day threats, threat management teams are equipped to inform and justify security decisions. Ememobong has served in the information technology industry for over ten years, and currently specialises in cyber threat management as a threat hunter and business threat defense strategist.
- USTLP:CLEAR
Reducing Ratio of Reserved But Public CVEs
 Shelby CunninghamShelby Cunningham (GitHub, US)
Shelby CunninghamShelby Cunningham (GitHub, US)
With the rise of the CVE Services API, low reserved-but-public (RBP) ratios are easier to obtain than the days when requesting CVEs was entirely manual. Requesting CVE IDs on an as-needed basis, rather than making a bulk CVE request at the start of the year, is an important practice for reducing RBP ratios. But it’s not the only practice. CNAs have multiple CVE reservation and publication practices available, such as publishing CVE records as soon as possible rather than waiting to publish CVE records in monthly or quarterly batches, to help reduce the number of reserved-but-public CVEs they have at any given time and avoid rejecting large numbers of CVEs at the end of the year. This talk discusses different practices and which kinds of CNAs may benefit from each practice, encouraging CNAs to combine practices to customize their RBP ratio reduction.
Shelby Cunningham is an advisory curator for the GitHub Advisory Database. Her duties include, but are not limited to, organizing and publishing vulnerability information for the GitHub Advisory Database and gathering vulnerability information from project maintainers on GitHub to submit to the CVE list. Working for a team with the responsibilities of a CVE Numbering Authority and a vulnerability database leads to her seeing a wide range of practices in vulnerability information disclosure. Prior to joining GitHub, Shelby wore a variety of hats at music label, distributor, and retailer Get Hip Recordings in Pittsburgh, PA.
- USTLP:CLEAR
SBOMs – The Missing Link
 Cassie CrossleyCassie Crossley (Schneider Electric, US)
Cassie CrossleyCassie Crossley (Schneider Electric, US)
There is some debate as to how SBOMs can enhance vulnerability management practices, and some believe that collecting SBOMs from internal teams or suppliers is too difficult and time-consuming. Learn how Schneider Electric has collected thousands of our product SBOMs and how we are leveraging the SBOMs as part of our corporate product CERT to quickly analyze and focus our attention when time is of importance. This presentation describes how we modified our policies and processes to collect, generate, and store thousands of SBOMs. You will hear how we have leveraged SBOMs during the Log4j and OpenSSL vulnerability events. Then we will conclude with key learnings, suggestions, and opportunities for improvement.
Cassie Crossley, Vice President, Supply Chain Security in the global Cybersecurity & Product Security Office at Schneider Electric, is an experienced cybersecurity technology executive in Information Technology and Product Development and
author of Software Supply Chain Security: Securing the End‐to‐End Supply Chain for Software, Firmware, and Hardware. She has many years of business and technical leadership experience in supply chain security, cybersecurity, product/application security, software/firmware development, program management, and data privacy.
Cassie has designed frameworks and operating models for end‐to‐end security in software development lifecycles, third party risk management, cybersecurity governance, and cybersecurity initiatives. She is a member of the CISA SBOM working groups and presents frequently on the topic of SBOMs and Supply Chain Security.
Cassie has held previous positions at Ceridian, Hewlett‐Packard, McAfee, Lotus, and IBM. She has an M.B.A. from California State University, Fresno, and her Bachelor of Science degree in Technical and Professional Communication with a specialization in Computer Science.
- BETLP:CLEAR
Sigma Unleashed: A Realistic Implementation
 Mathieu Le CleachMathieu Le Cleach (CERT-EU, BE)
Mathieu Le CleachMathieu Le Cleach (CERT-EU, BE)
Mathieu is a member of CERT-EU's Digital Forensics and Incident Response team. He has two hats: respond to security incidents, including significant ones, and engineer CERT-EU's detection strategy. Before joining CERT-EU, Mathieu worked as a CSIRT analyst for a French financial institution.
Sigma is a well-known generic detection rule format in the cybersecurity landscape. While this free, open-source project is very active and offers a wide range of features, its implementation is challenging, and especially for MSSPs. At CERT-EU, we serve the 90 European Union institutions, bodies, offices and agencies (Union entities) and we strive to deliver the best possible services to them. This is why we relentlessly try to enhance the detection capabilities of our Security Log Monitoring Service. To this endeavour, we created droid, a tool that we specifically built to introduce Detection-as-Code in our environment. In the spirit of fostering a culture of collective progress, we are very excited to share droid as our take to facilitate the ingestion of Sigma rules for any organisation. The tool unlocks the following use cases: detection content versioning, vendor agnostic approach, cross-tool detection content, testing and validating detection rules, by taking advantage of Atomic Red Team, automation of exporting the rules to multiple SIEMs and EDRs.
- JP ESTLP:CLEAR
So Far and Yet so Close. A Story of Collaboration Between Japan and Spain While Analyzing Simultaneous Infostealers Campaigns
 Masato Ikegami
Masato Ikegami Josep AlborsMasato Ikegami (Canon IT Solutions Inc., JP), Josep Albors (Ontinet.com, ES)
Josep AlborsMasato Ikegami (Canon IT Solutions Inc., JP), Josep Albors (Ontinet.com, ES)
Masato Ikegami is a malware analyst at Canon IT Solutions with 10 years of experience in cybersecurity. His primary focus is on the automated analysis and classification of malware. He currently holds the following certifications: CISSP, GREM, GCTI, GCIH.
Josep Albors is the Head of Awareness & Research at ESET Spain (Operated by Ontinet.com). He has more than 18 years’ experience in cybersecurity and now specializes in security awareness. He is also the editor at the ESET Spain blog and one of the contributors to the international ESET blog WeLiveSecurity.
He participated as a speaker at the AVAR 2019 international conference in Osaka, CARO Workshop 2023 in Bochum (Germany)and at many important local security conferences in Spain. Josep is a teacher in cybersecurity courses at several Spanish universities. He collaborates with the Spanish Guardia Civil, Spanish National Police and the Spanish Army, and teaches their units how to fight cybercrime.
Malware doesn’t know about frontiers but some malicious campaigns are more effective in some countries rather than others. When one of these countries is the one you are living in you might have a seriuos problem, specially if you work in cybersecurity. Luckily for us, we live in a connected world and you can find a colleague that is also facing the same problem in his country and work together with him, even if you are more than 10.000 Km away. This is the story and lessons learned of two researchers working together, facing several infostealer campaigns targeting Japan and Spain and how they started sharing information that helped them understand why the cybercriminals were so focused on their countries. This is also an example on how to create and maintain a collaboration channel between two distant countries that can be used as an example if you are facing similar problems.
- CATLP:CLEAR
Solving CTI Sector Incoherence in a Living Growing OpenCTI Repository: Extend STIX 2.1 FTW
Philippe Lin (Trend Micro, CA)
This talk discusses the challenges and complexities of running OpenCTI with dozens of contributors over a course of three years. We delve into the "organic chaos" caused by label misuse, duplicated entries, missepelling, and the confusion that arises from ingesting many external sources, such as SecureList, Palo Alto Unit42, and Trend Micro Research into OpenCTI. Using concrete examples, we illustrate how data cleansing became mission highly-impossible and hinder threat researchers. We discuss our efforts to standardize sector labels, our consideration on US CISA vs STIX, and the need to extend existing vocabularies like STIX 2.1. In conclusion, we share our best practices, tips, tricks and traps in updating OpenCTI data on a production system.
Philippe Lin is a Senior Threat Researcher at Trend Micro Research. His work revolves around industrial embedded systems, software-defined radio, 4G/5G core network and machine learning. He is an enthusiast of open-source software.
- AUTLP:CLEAR
The Trials and Tribulations of Bulk Converting CVEs to OSV
 Andrew PollockAndrew Pollock (Google Open Source Security Team, AU)
Andrew PollockAndrew Pollock (Google Open Source Security Team, AU)
Join Andrew Pollock, from Google’s Open Source Security Team, on a light-hearted and personally vulnerable (ha! see what I did there?) retrospective on what happens when you take a Security Engineer converting to Software Engineering, who last touched CVEs in any way shape or form 20 years ago, and get them to ramp up on a new project, that’s developed completely differently to anything internal at Google.
Andrew Pollock is a Senior Software Engineer on Google’s Open Source Security Team, working on OSV.dev. He recently worked on converting CVEs in the National Vulnerability Database relating to Open Source software vulnerabilities into the OSV schema. As a result, he discovered a hitherto unknown passion for data quality in CVE records."
- ESTLP:CLEAR
Tracking Threat Actors Using Images: A Hunting & Analysis Approach
 Joseliyo SánchezJoseliyo Sánchez (VirusTotal - Google, ES)
Joseliyo SánchezJoseliyo Sánchez (VirusTotal - Google, ES)
Images are a common feature of documents, but they can also be a valuable source of intelligence for security analysts. By tracking the images that threat actors use in their documents, analysts can gain insights into their procedures, as well as their potential targets and impersonated companies.
This type of approach has helped us find and track the Russian cyber espionage group Gamaredon and others such as the group known as Blind Eagle that is suspected to be from Latin America and other APTs/Crime groups. It will also discuss the challenges and limitations of the approach.
Joseliyo Sanchez is a security engineer at VirusTotal - Google. Member of the ENISA Working Group on Cyber Threat Landscapes. Previously worked at McAfee and BlackBerry as a threat researcher. His main objectives are threat hunting that leads to detection engineering and analysis of APTs and Crime groups.
- TW
Understanding Criminal Business Behind Supply Chain Attacks on Android
 Fyodor YarochkinFyodor Yarochkin (Trend Micro, TW)
Fyodor YarochkinFyodor Yarochkin (Trend Micro, TW)
Fyodor Yarochkin is a Senior Researcher, Forward-Looking Threat Research Senior at Trend Micro with a Ph.D. from EE, National Taiwan University. An early Snort Developer and Open Source Evangelist as well as a Programmer, his professional experience includes several years as a threat investigator and over eight years as an Information Security Analyst.
This presentation is for FIRST Members only, authentication is required on FIRST Portal to preview the video.
Understanding Criminal Business Behind Supply Chain Attacks on Android
February 16, 2024 11:30-17:00
- TW
Use and abuse of residential proxy networks
 Fyodor YarochkinFyodor Yarochkin (Trend Micro, TW)
Fyodor YarochkinFyodor Yarochkin (Trend Micro, TW)
Dr. Fyodor Yarochkin is a Senior Researcher, Forward-Looking Threat Research Senior at Trend Micro with a Ph.D. from EE, National Taiwan University. An early Snort Developer and Open Source Evangelist as well as a Programmer, his professional experience includes several years as a threat investigator and over eight years as an Information Security Analyst.
Fyodor Yarochkin discusses the evolving landscape of cybercrime, particularly the shift from traditional bulletproof hosting services to residential proxies. Researchers, including himself, have noted a growing caution in discussing these entities publicly. Residential proxies are easier and cheaper to maintain and present more complex challenges for defenders because they complicate traffic filtering.
Yarochkin has created a framework, termed a "residential proxy honeypot," to analyze traffic patterns from these proxies. He emphasizes the importance of understanding how these networks operate to effectively monitor and mitigate abuses.
He notes that the residential proxy ecosystem is diverse, featuring numerous small providers alongside larger companies, and highlights the varied marketing strategies used, including black hat forums and Telegram channels. The languages supported by proxy providers often reflect their target customer bases.
Finally, he concludes that there are no truly "good" residential proxy providers, as they all facilitate the bypassing of restrictions, raising ethical concerns about their operations.
This presentation is for FIRST Members only, authentication is required on FIRST Portal to preview the video.
Use and abuse of residential proxy networks
September 25, 2024 09:00-09:30
- US
Welcome & Introduction to FIRST
 Gavin ReidGavin Reid (HUMAN Security, US)
Gavin ReidGavin Reid (HUMAN Security, US)
Gavin Reid Gavin Reid serves as the CISO for HUMAN Security, a cybersecurity company that specializes in safeguarding enterprises from digital attacks while preserving digital experiences for users. In addition, he leads the Satori Threat Intelligence and Research Team as VP of Threat Intelligence.
Gavin began his cybersecurity career in information security at NASA's Johnson Space Center. He later went on to create Cisco's Security Incident Response Team (CSIRT), Cisco's Threat Research and Communications (TRAC), and Fidelity's Cyber Information Group (CIG). Before joining HUMAN, Gavin served as the CSO for Recorded Future, where he was responsible for ensuring the protection, integrity, confidentiality, and availability of all customer-facing services, internal operational systems, and related information assets. For more than 20 years, Gavin has managed every aspect of security for large enterprises.
- US
What defines the field of Cyber Threat Intelligence and its disciplines?
 Krassimir Tzvetanov, PhDKrassimir Tzvetanov, PhD (Purdue University, US)
Krassimir Tzvetanov, PhDKrassimir Tzvetanov, PhD (Purdue University, US)
For the past five years Krassimir Tzvetanov has been a graduate student at Purdue University focusing on Homeland Security, Threat Intelligence, Operational Security and Influence Operations, in the cyber domain.Before that, Krassimir was a security engineer at a small CDN, where he focused on incident response, investigations and threat research.
Previously he worked for companies like Cisco and A10 focusing on threat research and information exchange, DDoS mitigation, product security.
Before that Krassimir held several operational (SRE) and security positions at companies like Google and Yahoo! And Cisco.
Krassimir is very active in the security research and investigation community and has contributed to FIRST SIGs. He is also a co-founder and ran the BayThreat security conference, and has volunteered in different roles at DefCon, ShmooCon, and DC650.
Krassimir holds Bachelors in Electrical Engineering (Communications), Masters in Digital Forensics and Investigations, and Masters in Homeland security.
What defines the field of Cyber Threat Intelligence and its disciplines?
July 1, 2024 08:00-08:30
- USTLP:CLEAR
What It Takes to Lead America’s Vulnerability Management Team
 Bob Lord
Bob Lord Chris Hughes
Chris Hughes Lindsey Cerkovnik
Lindsey Cerkovnik Patrick Garrity
Patrick Garrity Sandy RadeskyBob Lord (CISA, US), Chris Hughes (Aquia, US), Lindsey Cerkovnik (CISA, US), Patrick Garrity (VulnCheck, US), Sandy Radesky (CISA, US)
Sandy RadeskyBob Lord (CISA, US), Chris Hughes (Aquia, US), Lindsey Cerkovnik (CISA, US), Patrick Garrity (VulnCheck, US), Sandy Radesky (CISA, US)
Do you ever wonder what the US Government does behind the scenes to synchronize vulnerability management operations? In this panel, we will have CISA’s Vulnerability Management Associate Director, Sandy Radesky, lead a panel discussion with both government and industry leaders in this space. We’ll share the effort it takes to coordinate with partners, reasons why we continue to lead as a collaborative community. We’ll discuss major efforts, to include some new ones: Secure by Design, Coordinated Vulnerability Disclosure, KEV, Open Source Security, and some of our newly released vulnerability analysis.
Bob Lord is a Senior Technical Advisor at the Cybersecurity and Infrastructure Security Agency (CISA). Previously he was the Chief Security Officer at the Democratic National Committee where he brought more than 20 years of experience in the information security space to the Committee, state parties, and campaigns. Before that he was Yahoo’s Chief Information Security Officer, covering areas such as risk management, product security, security software development, e-crimes and APT programs. He was the Chief Information Security Officer in Residence at Rapid 7, and before that headed up Twitter’s information security program as its first security hire.
Chris Hughes is the Co-founder and President, Aquia, a Cybersecurity consulting firm. Chris brings nearly 20 years of IT and cybersecurity experience to his role as co-founder and President at Aquia. Chris also serves as a Cyber Innovation Fellow (CIF) at the Cybersecurity Infrastructure and Security Agency (CISA) focusing on software supply chain security. Additionally, Chris advises various tech startups, including serving as the Chief Security Advisor at Endor Labs.
As a United States Air Force veteran and former civil servant in the U.S. Navy and the General Services Administration’s FedRAMP program, Chris is passionate about making a lasting impact on his country and our global community at large.
In addition to his public service, Chris spent several years as a consultant within the private sector and currently serves as an adjunct professor for cybersecurity master’s programs at the University of Maryland Global Campus. Chris participates in industry working groups, such as the Cloud Security Alliance’s Incident Response and SaaS Security Working Group, and serves as the Membership Chair for Cloud Security Alliance D.C. He is the co-host of the Resilient Cyber Podcast and runs the Resilient Cyber Substack where he shares episodes as well as detailed articles on topics such as Cloud, Vulnerability Management, DevSecOps and more.
Lindsey Cerkovnik is the Chief of CISA’s Vulnerability Response & Coordination (VRC) Branch. Her team is responsible for CISA’s Coordinated Vulnerability Disclosure (CVD) process, the Known Exploited Vulnerabilities (KEV) catalog, and CISA’s Stakeholder Specific Vulnerability Categorization (SSVC) process. Lindsey and her team help to maintain, support, and advance the global vulnerability ecosystem by funding and overseeing the CVE and CVE Numbering Authority (CNA) programs, leading the production and dissemination of machine-readable vulnerability enrichment information, and engaging in valuable technical collaboration with the vulnerability research community.
Patrick Garrity is a security researcher at VulnCheck where he focuses on vulnerabilities, vulnerability exploitation and threat actors. Patrick Garrity is a seasoned cybersecurity professional with over 15 years of experience helping build high-growth SaaS cybersecurity companies including VulnCheck, Nucleus Security, Blumira, Censys and Duo Security.
Sandy J. Radesky serves as the Associate Director for Vulnerability Management at the Cybersecurity and Infrastructure Security Agency (CISA). Prior to this role, Ms. Radesky served as the Deputy Command Information Officer (CIO) for U.S. Fleet Cyber Command/ U.S. TENTH Fleet from December 2020 to February 2023. In this position she oversaw the cybersecurity, policy, design, and future plans for the Navy in order to support full spectrum Cyberspace Operations to enable FLTCYBERCOM as the central operating authority for Navy Networks. Her efforts continued to improve, integrate and directly support joint warfighters, national-level leaders, and other mission and coalition partners across the full spectrum of global operations.
- ILTLP:CLEAR
Why Can't We All Just Get Along? Bridging the Gap in Vulnerability Prioritization Standards
 Yotam PerkalYotam Perkal (Rezilion, IL)
Yotam PerkalYotam Perkal (Rezilion, IL)
In the dynamic realm of vulnerability management, the proliferation of standards and frameworks like CVSS (Common Vulnerability Scoring System), EPSS (Exploit Prediction Scoring System), and VISS (Vulnerability Information and Severity Score) often leads to confusion, fragmentation, and inconsistency. This talk explores the underlying tensions between these standards, particularly in the context of vulnerability prioritization.
Our journey begins with an exploration of each framework, highlighting their unique methodologies, strengths, and limitations.
Then, we will center our discussion around the Strategic Stakeholder-Specific Vulnerability Categorization (SSVC), a framework that can act as a unifying bridge in this fragmented landscape. We will dissect how SSVC's adaptable and stakeholder-specific approach can harmonize these varying standards, providing a more cohesive and comprehensive vulnerability management strategy.
Key aspects of this talk include:
- A comparative analysis of CVSS, EPSS, and VISS, underscoring their operational divergences and impacts on cybersecurity decision-making.
- An in-depth exploration of SSVC's methodology, focusing on its flexible decision trees that accommodate diverse stakeholder needs and environmental contexts.
- A proposed roadmap for organizations looking to synergize these frameworks effectively, leveraging SSVC's adaptability.
In conclusion, this talk aims not just to highlight the challenges posed by the diversity of standards in vulnerability management but to offer a pragmatic and unifying solution through SSVC, paving the way for a more harmonized and effective approach to vulnerability prioritization and management in the cybersecurity domain.
Yotam Perkal leads the vulnerability research team at Rezilion, focusing on research around vulnerability validation, mitigation, and remediation.
Prior to Rezilion, Yotam filled several roles at PayPal Security organization, dealing with vulnerability management, threat intelligence, and Insider threat. Additionally, Yotam takes part in several OpenSSF working groups around open-source security, several CISA work streams around SBOM and VEX, and is a member of the PyCon Israel organization committee.
Yotam is passionate about the intersection between Cyber Security and Machine Learning, whether it be using ML in order to help solve Cyber Security challenges or exploring the challenges in securing AI/ML applications.